What to Do If Your Binance.US Account Gets Hacked
When your crypto is stolen from a Binance.US account, the way you respond in the first hours and days can shape your ability to recover funds or bring a legal claim.
Binance.US has a formal process that every user must follow before filing an arbitration claim. Skipping these steps can seriously delay or even block your case.
This guide explains what to do next and how our firm helps clients navigate recovery, law enforcement, and arbitration.
-
Secure Your Accounts Immediately
If you still have access to your account, act fast:
- Change your email and passwords right away.
- Switch or reset your 2FA to an authenticator app (avoid SMS).
- Take screenshots of balances, withdrawals, login history, IP/device activity, TXIDs, and security settings.
- If your phone was SIM-swapped, call your carrier immediately to lock the account and get activity logs.
Why it matters: you’re building the factual record you’ll later use with Binance.US, law enforcement, and in arbitration.
-
File a Support Ticket with Binance.US
Open a Customer Support ticket. Include TXIDs, timestamps, suspicious IPs/devices, and request log preservation (auth logs, device IDs, IPs, API events).
Binance.US explains that the Support route is the first leg of the complaints path:
“If you have a complaint with BAM, you may, but are not required to, first open a ticket with Customer Support and work with Customer Support to resolve your issue.” Terms of Use
Save the ticket number—you’ll need it for the complaint stage.
-
File Law-Enforcement Reports
When crypto is stolen, Binance.US will not provide account or transaction records directly to victims — even if it involves your own account. Their Law Enforcement Guide makes clear that such information is only available to U.S. law enforcement and government agencies through formal legal process.
That’s why filing with the right agencies immediately is critical.
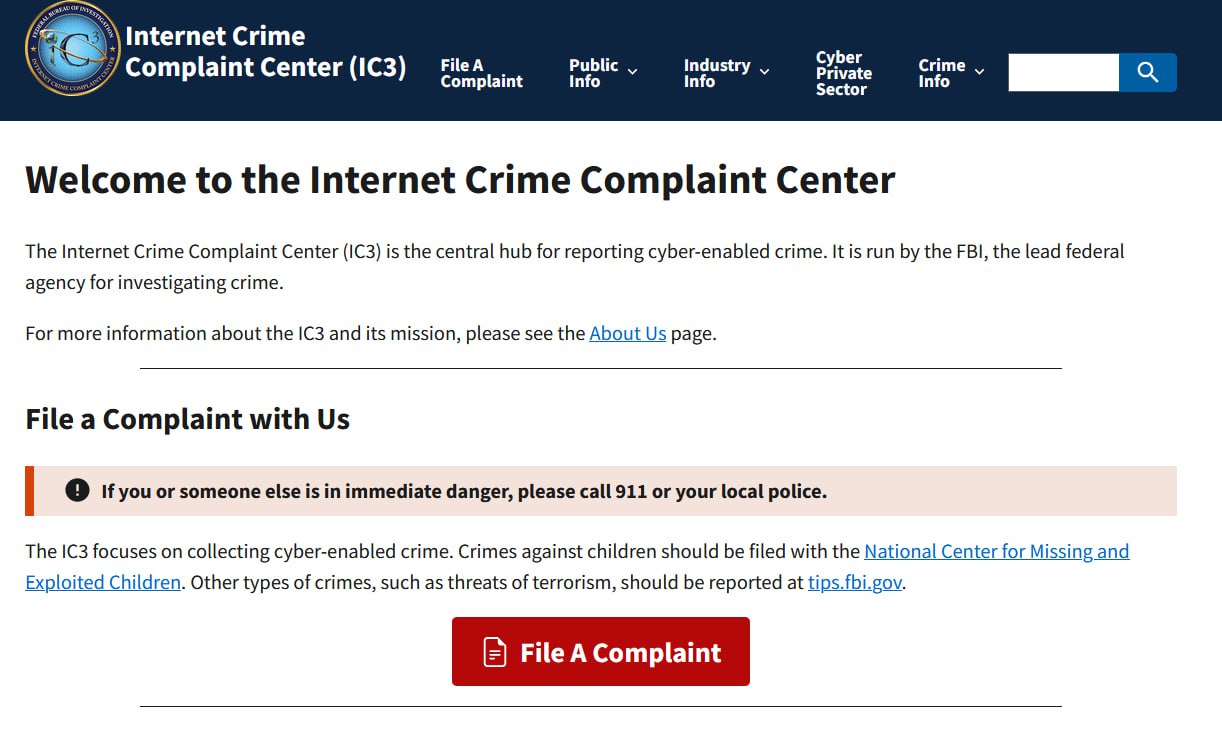
- File an online report with the FBI Internet Crime Complaint Center (IC3).
- File a Local Police Report.
- Provide Law Enforcement With Binance.US Guidance. Binance.US publishes a Law Enforcement Guide that explains exactly how police or federal agencies should request records.
Why this matters: Binance.US publishes a Law Enforcement Guide describing how U.S. agencies can request records; they respond to valid legal process from law enforcement—not to private requests. Share this link with your detective or agent.
-
File a Formal Complaint with Binance.US
If Support doesn’t resolve the issue, the next required step is to email resolutions@binance.us.
Your complaint must include:
- Your Support ticket number.
- A clear description of the problem.
- How you’d like Binance.US to resolve it.
- Any relevant documentation or evidence.
“Once you have already done so, and Customer Support has been unable to resolve your issue, please email your complaint to resolutions@binance.us […] provide your Customer Support ticket number, state the cause of your complaint, how you would like us to resolve the complaint […] Without a Customer Support ticket, we will not be able to respond meaningfully to your complaint email.”
Binance.US states:
“Within thirty business days […] the Complaint Officer may: (1) offer to resolve your complaint in the way you have requested; (2) reject your complaint and set out the reasons for the rejection; or (3) offer to resolve your complaint with an alternative proposal or solution.”
Important: Without a Support ticket, Binance.US will not process your complaint.
This step creates an official record with their Complaint Officer, which is a required stage before arbitration.
-
Send a Notice of Dispute (Pre-Arbitration Requirement)
Once you’ve filed a formal complaint and either received a denial or no resolution, the next step required by Binance.US’s Terms of Use is to send a formal “Notice of Dispute.”
This step is not optional — it is a contractual prerequisite to arbitration. If you don’t send this notice correctly, Binance.US can move to dismiss or delay your arbitration claim.
What to Include in the Notice of Dispute
Your email should include:
- Your full account details (name, phone, username, email).
- A short and clear summary of the issue, including key dates, TXIDs, ticket and complaint numbers.
- How you want Binance.US to resolve the claim (e.g., reimbursement, data disclosure, cooperation with law enforcement).
- Your lawyer’s contact information, if you have one.
Send your Notice to: legal@binance.us
This formal notice isn’t just a formality — it protects your ability to bring a legal claim.
- It triggers the 60-day “Informal Resolution Period” during which Binance.US must investigate the claim and can propose settlement.
- The statute of limitations is tolled (paused) during this period, preserving your legal rights.
- Under the arbitration clause, you cannot file for arbitration until this period ends. If you do, Binance.US can ask the arbitration forum or a court to stop the proceeding.
- Your Notice establishes a paper trail showing that you followed the Terms — something arbitrators often look for.
“Once a complete Notice of Dispute has been received, the recipient has 60 days to investigate the claims. If either side requests a settlement conference during this period, then you and us must cooperate to schedule that meeting by phone or videoconference. […] An arbitration cannot be filed until the Informal Resolution Period has ended.”
-
Move to Arbitration if Binance.US Doesn’t Resolve Your Claim
If your case is not resolved during the 60-day informal resolution period, the only legal path available under Binance.US’s Terms of Use is binding arbitration through the American Arbitration Association (AAA) under the Consumer Arbitration Rules. Arbitration is mandatory for customer disputes, and class actions are not allowed, which means each claim must be pursued individually.
Key Points About the Arbitration Process:
- Mandatory under the Terms of Use: Arbitration is required before any legal claim can proceed.
- Individual claims only: Class actions are waived, so each case is handled separately.
- Virtual proceedings: All hearings are held remotely.
- Streamlined for smaller claims: If the claim is under $25,000, the case may be decided on written submissions only, without a live hearing.
Arbitration is a formal legal process, and Binance.US will have experienced defense counsel. A knowledgeable attorney can ensure your claim is filed correctly, backed by strong evidence, and positioned to maximize your recovery.
-
Understand Exchange Liability
Binance.US, like most major crypto exchanges, disclaims responsibility for losses caused by hacks, phishing, or account takeovers. Unlike banks or traditional brokerages, crypto exchanges are not insured by the FDIC or SIPC — meaning there’s no government protection or automatic reimbursement if your funds are stolen or the platform fails.
This is why following Binance.US’s formal complaint and dispute process is essential. It preserves your legal rights and creates a clear record if the exchange failed to act reasonably or ignored security red flags. While recovery isn’t guaranteed, well-documented claims supported by law enforcement can significantly increase your leverage in negotiations or arbitration.
Contact Us
If your cryptocurrency was stolen from Binance.US due to an account takeover, SIM swap, or any other unauthorized breach, don’t wait to act.
With over six years of experience and a record of handling more than 100 consumer arbitration cases, our firm has pursued claims against major cryptocurrency exchanges as well as leading phone carriers such as Verizon, T-Mobile, and AT&T.
Our attorneys are experienced in navigating proceedings before AAA, JAMS, and NAM, and understand the procedural and strategic nuances that can make or break a case. We also represent victims whose assets were stolen not only from regulated exchanges but also from self-custody wallets like MetaMask and other decentralized platforms.
Time is critical in crypto theft cases. Swift, strategic legal action can make the difference between recovery and permanent loss.
Reach out to us today to discuss your case and legal options: (212) 457-9797 | info@dilendorf.com.
Attorney Advertising. Prior results do not guarantee a similar outcome. This information is provided for educational purposes and is not legal advice.
Attorney Max Dilendorf explains how U.S. courts treat Cook Islands asset-protection trusts, using the Ninth Circuit’s FTC v. Affordable Media, LLC (1999) as a guide.
In plain English, he covers what these trusts are, how “duress clauses” work, why judges order repatriation of assets, and how civil contempt and skepticism of “impossibility” defenses play out.
Key takeaways help families—and crypto holders—assess real enforcement risks before moving assets offshore. Dilendorf Law Firm offers confidential reviews of existing and proposed offshore structures.
When Michael Terpin’s SIM card was fraudulently swapped in January 2018, attackers gained control of his mobile number, intercepted password resets, accessed his cloud storage, and stole approximately $24 million in digital assets.
After years of litigation, Terpin v. AT&T is scheduled for jury trial in March 2026. This case is expected to play a pivotal role in defining the scope of telecom carriers’ responsibilities in SIM-swap incidents—and could give self-custody wallet users a viable legal path to recovery.
The Unique Challenges Faced by Self-Custody Wallet Users
Victims of SIM-swap attacks who store digital assets in self-custody wallets such as MetaMask, Trust Wallet, or hardware wallets face significant legal obstacles:
- No custodian to recover funds. Because self-custody wallets are non-custodial, no entity holds the assets or has the ability to reverse unauthorized transactions.
- Limited claims against wallet providers. Wallet software providers generally disclaim liability and are not responsible for losses resulting from theft.
- Exchanges often are not involved. In many cases, stolen assets never touch a regulated exchange, leaving victims with no practical recovery option.
- Barriers under state law. Negligence or contract claims against carriers are often blocked by liability waivers and the economic loss rule.
The Terpin case changes this legal landscape by focusing on a federal statutory duty under the Communications Act.
Section 222: A Federal Privacy Duty
Section 222 of the Communications Act of 1934 (47 U.S.C. § 222) requires telecom carriers to protect the confidentiality of Customer Proprietary Network Information (CPNI).
In September 2024, the Ninth Circuit ruled that a carrier may violate Section 222 not only by directly disclosing CPNI but also by “permitting access” to it through inadequate authentication procedures.
If a carrier approves a SIM swap without taking reasonable measures to verify identity, it may be held liable under federal law. On July 16, 2025, the district court partly denied AT&T’s renewed summary-judgment motion on the Section 222 claim, clearing the case for trial.
“[…] there is sufficient evidence before the Court for a reasonable juror to find that AT&T failed to ‘take reasonable measures [. . .] to protect against’ unauthorized disclosure and ‘properly authenticate’ Terpin’s identity before allowing access to his CPNI via the fraudulent SIM swap.”
This is significant for self-custody wallet holders because Section 222 claims are not limited by contractual liability waivers and are not barred by the economic loss rule.
Why Carriers Are Often the Most Effective Legal Target
In SIM-swap incidents, the carrier is the critical control point. A fraudulent SIM change typically triggers the entire chain of events:
- Number is ported without proper verification.
- Attackers intercept SMS or email reset codes.
- Credentials or seed phrases are accessed through cloud or email accounts.
- Digital assets are stolen from self-custody wallets.
Because carriers control the SIM-swap process, they are often the most direct and practical defendant. Unlike wallet providers, carriers have a clear statutory duty and maintain authentication logs and procedures that can be challenged in litigation or arbitration.
The Central Questions at the 2026 Trial
The upcoming Terpin trial is expected to address several key issues:
- Causation: Whether a carrier’s failure to properly authenticate a SIM swap foreseeably leads to cryptocurrency theft.
- Scope of liability: How broadly courts will interpret “permitting access” under Section 222.
- Industry impact: Whether carriers must strengthen their SIM-swap protocols and authentication controls nationwide.
A Turning Point for SIM-Swap Victims
Terpin v. AT&T could establish a meaningful precedent for SIM-swap victims, particularly for individuals who lost assets from self-custody wallets.
For years, these victims had few options for recovery. Now, federal law under Section 222 provides a potential basis to hold carriers accountable when inadequate authentication allows attackers to compromise critical accounts.
Dilendorf Law Firm Representation
At Dilendorf Law Firm, we represent clients who have been targeted by SIM-swap attacks and other forms of cyber fraud.
With over six years of experience and a record of handling more than 100 consumer arbitration cases, we have successfully pursued claims against major cryptocurrency exchanges, such as Coinbase, and leading phone carriers such as Verizon, T-Mobile, and AT&T.
Our attorneys are skilled in navigating proceedings before all major arbitration forums, including AAA, JAMS, and NAM.
We also represent victims whose digital assets were stolen not only from regulated exchanges but also from self-custody wallets like MetaMask and other decentralized platforms.
In high-stakes cases, we advise and coordinate with U.S. law enforcement and investigative agencies—including the FBI, Department of Homeland Security (DHS), and the Secret Service—as part of broader recovery strategies and criminal investigations into cybercrime.
If you have suffered losses due to a SIM swapping incident or other cyber fraud, contact us to discuss your case and options for recovery.
Email: info@dilendorf.com | Phone: 212.457.9797
Disclaimer: This summary is based on public records and does not constitute legal advice. Dilendorf Law Firm is not counsel of record for Michael Terpin, and his case is in no way affiliated with our firm.
If your Coinbase account has been hacked, the first step is mandatory. Under Section 7 of Coinbase’s User Agreement, you should begin by contacting Coinbase Support and opening a ticket. This generates a case number, which is essential for the Formal Complaint process.
If the matter is not resolved through Support, the next step is to file a Formal Complaint with Coinbase. Submitting a Formal Complaint starts Coinbase’s 45-business-day response period. Coinbase will acknowledge receipt of your complaint and issue a written resolution notice after review.
Once that resolution notice is sent—or once 45 business days have passed without a resolution—the Formal Complaint process is considered complete. At that point, you may pursue arbitration if necessary.
In short: Support first, Formal Complaint second. This sequence is mandatory for Coinbase clients and is the only way to preserve your right to escalate a dispute with Coinbase.
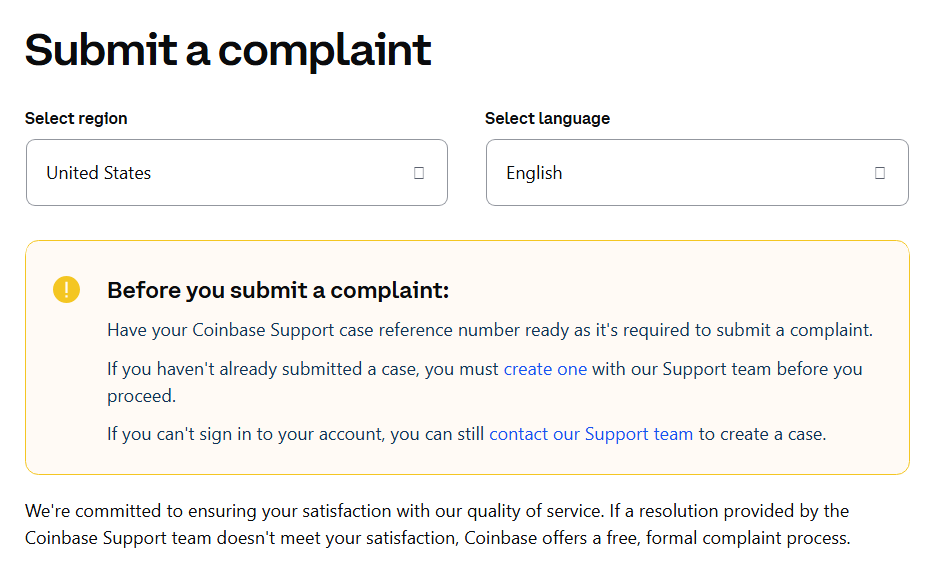
Step 1 — Notice Begins with Coinbase Support
The first step in giving notice is to contact Coinbase through its Support page. When you open a Support ticket, Coinbase assigns you a case number.
That case number is critical. It shows you gave proper notice and must be included in your Formal Complaint. Without it, your notice will be incomplete.
Step 2 — Notice Continues with the Formal Complaint
If the Support ticket does not resolve the matter, you must escalate by filing a Formal Complaint. This is still part of the required notice process. It tells Coinbase, in writing, that you are formally disputing the unauthorized activity and obligates them to respond.
Coinbase User Agreement, §7.2.1 Procedural Steps:
“In the event that the dispute is not resolved through your contact with Coinbase Support, you agree to use our complaint form to describe your dispute, how you would like us to resolve the complaint, and any other relevant information […]. The Formal Complaint Process is completed when Coinbase responds to your complaint or forty-five (45) business days after the date we receive your complaint, whichever occurs first.”
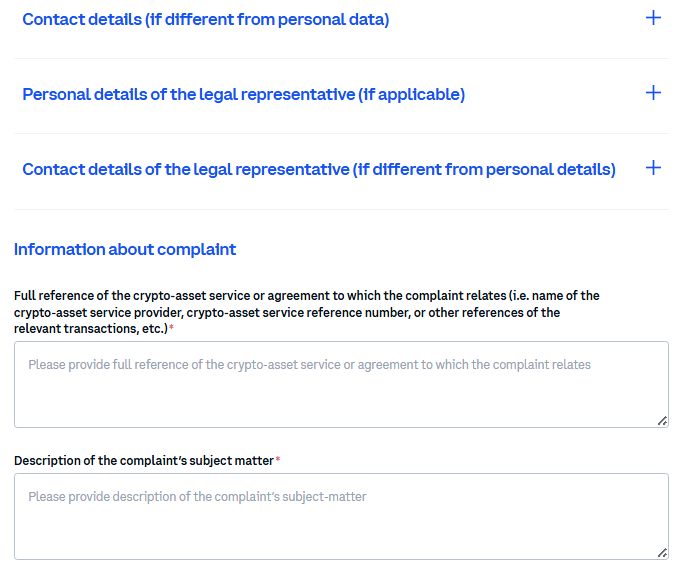
When you submit the complaint online, you will be asked to complete several required blocks, including:
- Personal data of the complainant — your name, contact details, and address.
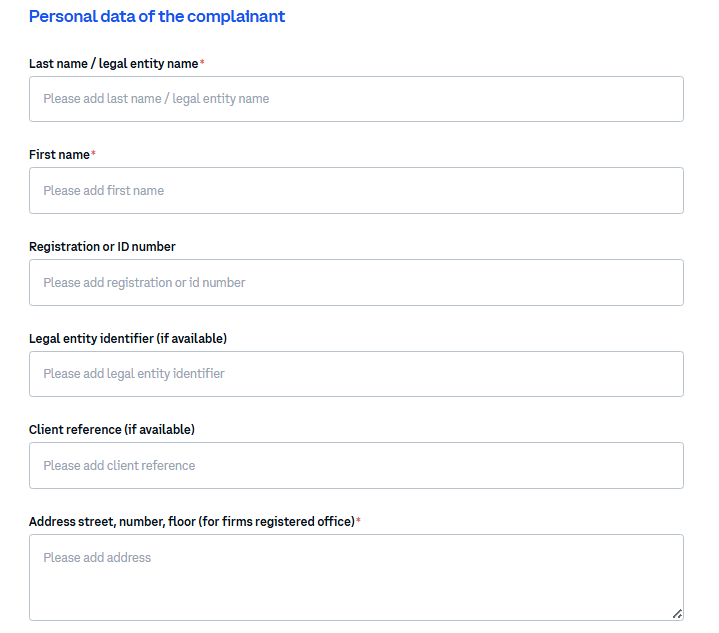
- Personal details of the legal representative (if applicable) — if an attorney is filing on your behalf, Coinbase requires a power of attorney or official proof of representation.
- Information about the complaint — this is where you must reference your Support case number, describe the unauthorized access, include dates and transaction IDs (TXIDs), and state what resolution you are requesting.
Step 3 — Resolution Notice and 45-Business-Day Timeline
After you submit a Formal Complaint, Coinbase must acknowledge receipt and review it. A Coinbase support representative will then issue a resolution notice.
The complaint process is considered complete when either:
- Coinbase sends the resolution notice, or
- 45 business days pass from the date Coinbase received your complaint.
Only once this process is complete may you pursue arbitration or small claims.
Why Proper Notice Matters
The Coinbase User Agreement makes clear: you cannot skip Support, and you cannot skip the Formal Complaint. Notice is the foundation of your claim. If you fail to provide notice in the exact way required, any arbitration or small-claims action may be dismissed.
“You must complete the Formal Complaint Process before filing any arbitration or small claims action. If you do not complete it, then you agree that your claim or action must be dismissed from arbitration or small claims court.” Coinbase User Agreement, §7.2.
Contact Us
At Dilendorf Law Firm, we focus on helping clients whose digital assets were stolen through hacked exchange accounts, SIM-swapping incidents, or compromised self-custody wallets such as MetaMask.
With over six years of experience and a record of handling more than 100 arbitration cases, we have pursued claims against Coinbase and other leading exchanges, as well as against major phone carriers like Verizon, T-Mobile, and AT&T. Our attorneys are well-versed in proceedings before AAA, JAMS, and NAM, the leading arbitration forums for crypto disputes.
We understand the urgency of these cases and guide clients step-by-step through Coinbase’s notice requirements—from the Support ticket and case number to the Formal Complaint and arbitration.
If your Coinbase account was hacked and your assets were stolen, contact us today to discuss your options for recovery: info@dilendorf.com | (212) 457-9797.
In the high-stakes realm of cryptocurrency investment, SIM swap fraud poses a severe threat, allowing hackers to hijack phone numbers and drain digital wallets. Victims often pursue negligence claims against phone carriers, alleging failures in security, employee oversight, and fraud prevention.
However, courts may decline these claims, often relying on the economic loss rule and the absence of an independent duty beyond contractual obligations.
The Terpin v. AT&T Mobility, LLC case, alongside other rulings, exemplifies this judicial trend.
Understanding Negligence in SIM Swap Cases
Negligence requires proving: (1) a duty of care; (2) breach of that duty; (3) causation; and (4) damages.
In SIM swap litigation, plaintiffs assert that carriers owe a duty to protect account security through robust PIN systems, employee training, and monitoring of authorized retailers.
Michael Terpin, in his August 2018 complaint, alleged negligence (Count 10), negligent supervision and training (Count 11), and negligent hiring (Count 12), claiming AT&T’s lapses enabled a $24 million crypto theft.
His Second Amended Complaint (SAC) in March 2020 refined these into Counts 5–7, emphasizing AT&T’s “strict duty” under federal law and its Privacy Policy to safeguard customer proprietary network information (CPNI).
Yet, courts often limit this duty to contractual terms. The economic loss rule bars recovery for economic damages (e.g., stolen cryptocurrency) absent physical harm or an independent tort duty, preserving contract law’s boundaries. Carriers argue their obligations end with service agreements, not tort liability.
Terpin v. AT&T: A Clear Dismissal of Negligence Claims
Terpin’s case stemmed from a January 2018 SIM swap—the second targeting his AT&T account. Hackers, led by Ellis Pinsky, bribed a Connecticut retailer employee to reassign Terpin’s number, intercepting password resets to access his OneDrive and cryptocurrency wallets.
Terpin’s 2018 complaint highlighted AT&T’s prior 2017 fraud awareness and inadequate response, while the SAC detailed the carrier’s failure to learn from a 2013 FCC consent decree fining it $25 million for data breaches.
The U.S. District Court for the Central District of California granted summary judgment on Terpin’s negligence claims in March 2023, finding no duty beyond the Wireless Customer Agreement.
The July 16, 2025, order reinforced this: “Plaintiff Michael Terpin sued Defendant AT&T Mobility LLC after bad actors gained control over his cell phone number through a fraudulent ‘SIM swap’ and used that control to steal his cryptocurrency. The Ninth Circuit affirmed dismissal of Terpin’s fraud and punitive damages claims and affirmed summary judgment for AT&T on Terpin’s negligence, breach of contract, and declaratory relief claims.” The court applied California’s economic loss rule, rejecting a fiduciary duty based on Terpin’s fraud history as a commercial, not special, relationship.
The Ninth Circuit’s September 2024 ruling (Terpin v. AT&T Mobility, LLC, 118 F.4th 1102 (9th Cir. 2024)) upheld this, stating Terpin’s negligence claims were “foreclosed” for lacking independence from the contract.
As the court explained in its opinion, “The panel affirmed the district court’s summary judgment on Terpin’s negligence claims […]” and emphasized that “Terpin’s negligence claims rest on AT&T’s alleged duty to adequately protect Terpin’s account information. But he fails to identify a duty ‘independent of’ the contract.”
The panel further stated, “To impose a tort duty in such circumstances would go further than creating obligations unnegotiated or agreed to by the parties; it would dictate terms that are contrary to the parties’ allocation of rights and responsibilities.” The court also declined to find an independent duty under Section 222 of the FCA, stating, “We decline to hold that Section 222 imposes a duty of care giving rise to a state-law negligence claim,” as no authority supported transforming the statutory confidentiality duty into a California negligence basis.
Only Terpin’s FCA claim, based on alleged unauthorized CPNI access, proceeded to remand.
Implications for Victims: Overcoming Legal Barriers
Negligence claims in Terpin faltered due to the economic loss rule, which requires an independent duty beyond the contract—a threshold not met despite Terpin’s prior fraud alerts.
Proximate cause also proved elusive, as the 2025 order noted: “Terpin does not seriously dispute that the FCA incorporates a proximate cause requirement.” This shifts focus to statutory remedies like the FCA, where the court found “Terpin raised a triable issue of material fact as to whether AT&T violated the FCA.”
Navigating legal differences across states can make things tricky. California’s strict economic loss rule often limits recovery to cases with physical damage, making it tough to win negligence claims for financial losses like stolen crypto.
In contrast, states like North Carolina or Washington sometimes take a more flexible approach, occasionally recognizing that carriers might have wider responsibilities in similar situations.
To boost your chances, keep detailed records of every interaction with your carrier—such as fraud reports, security upgrade requests, and employee responses. However, succeeding still hinges on finding solid legal grounds, like statutory protections or contract terms, which can be a challenge.
Contact Us
At Dilendorf Law Firm, we represent clients who have been targeted by SIM-swap attacks and other forms of cyber fraud.
With over six years of experience and a record of handling more than 100 consumer arbitration cases, we have successfully pursued claims against major cryptocurrency exchanges—including Coinbase—and leading phone carriers such as Verizon, T-Mobile, and AT&T.
Our attorneys are skilled in navigating proceedings before all major arbitration forums, including AAA, JAMS, and NAM.
We also represent victims whose digital assets were stolen not only from regulated exchanges but also from self-custody wallets like MetaMask and other decentralized platforms.
In high-stakes cases, we advise and coordinate with U.S. law enforcement and investigative agencies—including the FBI, Department of Homeland Security (DHS), and the Secret Service—as part of broader recovery strategies and criminal investigations into cybercrime.
If you have suffered losses due to a SIM swapping incident or other cyber fraud, contact us to discuss your case and options for recovery.
Email: info@dilendorf.com | Phone: 212.457.9797
This summary is based on public records and does not constitute legal advice. Dilendorf Law Firm is not counsel of record for Michael Terpin, and his case is in no way affiliated with our firm.
When a SIM swap or port-out happens, the carrier’s notices and internal records are your earliest, most objective evidence.
They show when the request was made, how it was authenticated, what the carrier told you (and when), and whether any account-lock was available or enabled.
If your crypto or funds were later stolen—from a self-custody wallet (MetaMask, Phantom) or a regulated exchange—those artifacts become the backbone of your case.
In arbitration, the decision maker isn’t guessing; they’re reconstructing a timeline: service loss → SIM/port change → login/reset events → withdrawals.
Carrier notices and logs anchor that timeline and help prove causation—that control of your number enabled password resets, SMS 2FA interception, or account recovery into your wallet or exchange.
They also speak to carrier compliance with required pre-change notifications and authentication, and they document your own reasonable steps to secure the account and respond quickly.
Practically, this evidence gives you leverage across the board: it helps exchanges escalate your claim, supports law-enforcement reports, and frames arbitration arguments about what should have happened versus what actually happened.
Preserve every notice and demand written confirmation from the carrier now; if you wait, logs roll off, memories fade, and your best proof disappears.
Dilendorf Law Firm has represented SIM-swap victims nationwide since 2019 and arbitrated 100+ crypto-cyber matters. Below is your playbook: what rules apply, what to request, and how to keep it admissible, organized, and useful for arbitration.
What Carriers Must Tell You
1) Pre-change notice for SIM swaps.
Federal rules require your wireless carrier to notify you before it completes a SIM change:
“Upon receiving a SIM change request, and before effectuating the request, a CMRS provider shall provide immediate notification to the customer that a SIM change request associated with the customer’s account was made, delivered in accordance with customer preferences, if indicated, and using means reasonably designed to reach the customer associated with the account and clear and concise language that provides sufficient information to effectively inform a customer that a SIM change request involving the customerer’s SIM was made, except if the SIM change request was made in connection with a legitimate line separation request pursuant to 47 U.S.C. § 345…”
2) Written proof of fraud on request.
If you’re a victim, you’re entitled to documentation from the carrier:
“Promptly provide customers, upon request, with documentation of fraudulent SIM changes involving their accounts.” Federal Communication Commission Report.
3) Account-lock option.
Carriers must offer a no-cost “lock” that blocks SIM changes until you unlock it:
“A CMRS provider shall offer customers, at no cost, the option to lock their accounts to prohibit… SIM change[s].” Federal Communication Commission Report.
4) Baseline account-change notice (long-standing rule).
Separate CPNI rules require immediate notice when certain account details are changed:
“Telecommunications carriers must notify customers immediately whenever a password… online account, or address of record is created or changed.” 47 CFR Parts 52 and 64.
5) Port-out (number transfer) protections.
For number port-outs, carriers must authenticate you before the port:
“A CMRS provider shall use secure methods to authenticate… before effectuating a port-out request.” 47 CFR § 52.37
The FCC also adopted pre-port notice:
“…require wireless providers to provide immediate notification… whenever a port-out request is made… before a provider effectuates a port.” Federal Communications Commission Report – in the Matter of Protecting Customers from Sim Swap and Port Out Fraud.
6) The statute behind these rules.
All of this sits on 47 U.S.C. § 222, which imposes a general duty:
“Every telecommunications carrier has a duty to protect the confidentiality of… customers…”
If you didn’t receive a pre-change notice, what to demand (in writing)
If your number was hijacked (SIM swap or port-out) and crypto was drained from a self-custody wallet (MetaMask or Phantom) or a regulated exchange:
Ask the carrier (in writing) for:
- Event confirmation with timestamps
- The exact date/time of the SIM change or port-out and how it was processed (in-store, app, online, call).
- Cite the notice rule: “before effectuating the request… provide immediate notification.” Save the carrier’s explanation of what was or wasn’t sent.
- Authentication details used
- What method(s) the carrier used to verify identity. (For port-outs, the carrier must use secure methods “before effectuating” the port.)
- Copies/logs of the customer notice
- When the notice was sent, to which destination(s), and the content/template used (you’re checking the “means reasonably designed to reach the customer” and clear language).
- Fraud documentation letter
- Request the rule-based fraud documentation (“promptly provide customers, upon request, with documentation of fraudulent SIM changes”). This is critical evidence for exchanges and arbitration.
- For port-outs, the FCC likewise required prompt documentation for victims in its order.
- Account-lock status
- Ask whether an account/SIM lock was available and active; the rule says carriers must offer a no-cost lock to block SIM changes.
Preserve everything for exchanges and arbitration
Create one folder and save:
- Carrier notice(s), carrier written responses, case/ticket numbers.
- Timestamps for service loss, SIM/port event, logins, withdrawals.
- Exchange TXIDs, login IPs/devices, and support emails.
- IC3 and police reports, plus any forensic or device-remediation reports.
Arbitrators and exchange fraud teams will expect to see: (a) what the carrier should have sent before the change; (b) what was actually sent; and (c) the written documentation of fraud the rules say you can request.
Need help? Free consultation for SIM-swap victims
If you were the victim of a SIM swap or device/phone takeover through Verizon, AT&T, or T-Mobile and your crypto was stolen from a self-custody wallet (e.g., MetaMask, Phantom, etc.) or a regulated exchange (e.g., Coinbase, Kraken, Binance, Uphold, Crypto.com), contact Dilendorf Law Firm for a free, confidential consultation.
We’re NY-based, represent clients nationwide, and have 6+ years arbitrating complex crypto-cyber matters, including SIM-swap disputes against major U.S. carriers and exchange-related claims.
We’re NY-based, represent clients nationwide, and have 6+ years arbitrating complex crypto-cyber matters, including SIM-swap disputes against major U.S. carriers.
We can help you:
- Demand and preserve carrier notices and fraud documentation (e.g., under 47 C.F.R. §§ 64.2010(h), 52.37).
- Organize exchange records and on-chain evidence.
- Prepare IC3/police filings and an arbitration-ready timeline.
- Evaluate your legal options and map a strategy.
Contact: info@dilendorf.com | | (212) 457-9797
Attorney Advertising. Past results do not guarantee a similar outcome.
If your crypto was stolen from a U.S. exchange such as Coinbase, Uphold, Binance or Kraken, you might be wondering: What was the exchange supposed to do to protect me?
New York’s BitLicense rules are widely seen as the country’s gold standard for crypto consumer protection. Many large exchanges serve New Yorkers and therefore follow New York’s standards across their whole platform—no matter where you live.
Bottom line: Even if you’re not in New York, you can still point to these expectations when you talk to the exchange or prepare an arbitration claim.
Who This Applies To
The New York Department of Financial Services (NYDFS) says the guidance applies to “all virtual currency business entities that are either licensed under 23 NYCRR Part 200 or chartered as a limited purpose trust company under the New York Banking Law (the ‘VC Entities’).”
If an exchange operates in New York, it’s under this umbrella and is expected to meet these standards. In practice, large exchanges typically use the same controls nationwide, not a weaker version for non-NY customers.
What the Standard of Care Looks Like
1) Detect, Prevent, and Respond to Fraud
NYDFS: “VC Entities are required to implement measures designed to effectively detect, prevent, and respond to fraud, attempted fraud, and similar wrongdoing; and market manipulation is a form of wrongdoing about which VC Entities must be especially vigilant….”
What this means for you: Exchanges should have tools that spot risk early, block or hold suspicious activity, and move fast when something looks wrong (unusual logins, new devices, sudden withdrawals).
These protections should work on both the front end (login/withdrawal security) and the back end (monitoring, alerting, holds).
2) A Real, Written Anti-Fraud Program
NYDFS requires “effective implementation of a written policy that: identifies and assesses the full range of fraud-related and similar risk areas… provides effective procedures and controls… allocates responsibility for monitoring risks; and provides for periodic evaluation and revision….”
What this means for you: There should be a living playbook that covers real threats like phishing, SIM-swaps, device takeovers, and social engineering.
These security features should be paired with concrete protections such as phishing-resistant 2FA, device binding, cooldowns after password resets, withdrawal holds/allow-lists, and on-chain risk screening—with named owners responsible and regular updates as scams evolve.
3) Effective Investigation of Suspected or Actual Wrongdoing
NYDFS: “A VC Entity must provide for the effective investigation of fraud and other wrongdoing, whether suspected or actual….”
What this means for you: When you report theft, the exchange shouldn’t just send boilerplate emails.
It should pull login/IP/device logs, review risk flags, explain why withdrawals were allowed, and document what it did. You’re entitled to ask what steps they actually took.
4) Prompt Reporting to NYDFS and Ongoing Follow-Ups
NYDFS says:
• “Immediately upon the discovery of any wrongdoing, a VC Entity must submit to the Department a report stating all pertinent details….”
• “The Department expects … the first further report … within 48 hours after submission of the original report….”
• “A VC Entity must maintain … records of each incident….”
• “When submitting required reports… use: vcreports@dfs.ny.gov
5) Quick Tips for Victims
• Lock down your accounts immediately: Change passwords (email + exchange), switch to an authenticator app (not SMS), and revoke unknown devices/sessions.
• Call your carrier: Add/confirm a port-out/SIM-swap PIN; ask if there were recent SIM changes.
• Preserve evidence: Save TXIDs, wallet addresses, timestamps, screenshots, emails, chat logs, and create a simple timeline of events.
• File an IC3 report (ic3.gov): Keep the confirmation number with your case file.
• Be cautious with “recovery” offers: Avoid anyone guaranteeing results or demanding big upfront fees.
Conclusion
Arbitrating or litigating a crypto-theft claim is high-risk and difficult. Most exchanges require arbitration and embed terms that shift risk to users, limit remedies, and set strict procedures.
If your funds were stolen, speak with experienced counsel as early as possible to protect your rights and build a strong, fact-driven record.
About Max Dilendorf
Max Dilendorf represents victims nationwide against Coinbase, Kraken, Binance, and Uphold, and SIM-swap victims against T-Mobile, AT&T, and Verizon whose self-custody wallets (e.g., MetaMask) were drained.
With 6+ years in this space, Max has arbitrated crypto disputes across AAA, JAMS, and NAM—handling demand drafting, 100+ crypto-related discovery disputes (motions to compel/protective orders, subpoenas, ESI, privilege), expert coordination, depositions, and taking cases through final evidentiary hearings.
When crypto is stolen from a hosted exchange account, does the Electronic Fund Transfer Act (EFTA) apply? Two Southern District of New York judges—ruling just twelve days apart on cases against Uphold, a custodial cryptocurrency platform—gave very different answers.
The Split Decisions
- August 11, 2023 — Yuille v. Uphold HQ Inc. (Judge Lewis J. Liman), Case No. 1:22-cv-07453-LJL
Judge Liman held that the plaintiff’s Uphold account was not an EFTA “account” because it was opened primarily for investment. On that basis, the court did not decide whether crypto counts as “funds” under the statute. - August 23, 2023 — Nero v. Uphold HQ Inc. (Judge Denise Cote), Case No. 22-cv-1602 (DLC)
Judge Cote read EFTA broadly, rejected the idea that a profit motive disqualifies a consumer account, and allowed the EFTA claim to move forward (though she dismissed actual damages at the pleadings stage).
What the statute says (15 U.S.C. § 1693a)
- “Electronic fund transfer.”
“Any transfer of funds […] initiated through an electronic terminal, telephonic instrument, or computer […] so as to order, instruct, or authorize a financial institution to debit or credit an account,” with specific exclusions (e.g., certain securities or commodities transactions). 15 U.S.C. § 1693a(7). - “Account.”
“A demand deposit, savings deposit, or other asset account … established primarily for personal, family, or household purposes.” 15 U.S.C. § 1693a(2).
EFTA and Regulation E impose strict error-resolution duties and can award enhanced damages when an institution fails to investigate in good faith or to provisionally recredit. 15 U.S.C. §§ 1693f, 1693m(a).
Position A — Nero (Judge Denise Cote)
- “An asset account covered by the EFTA may be an account holding investments from which the individual hopes to gain a profit for herself or her family.”
- “Only the transactions involving the purchase and sale of regulated securities are excluded; the asset accounts holding those investments are not excluded.”
- “The fact that Congress has not amended the EFTA to add an explicit reference to cryptocurrency does not alter the Court’s duty to construe the statute as written.”
For Judge Cote, EFTA is technology-neutral. A personal account doesn’t lose protection just because it is also used for investing.
Note: The Nero case later settled in October 2024, with approval of $500,000 in statutory damages plus $320,000 in fees/administration — $820,000 total.
Position B — Yuille (Judge Lewis J. Liman)
- “The Court […] need not determine whether the term ‘funds’ […] includes cryptocurrency […] because the Court finds that the Account is not an ‘account’ within the meaning of the EFTA.”
- “The purpose for which the Account was established was for investment, which has an inherent profit motive.”
Judge Liman highlighted the plaintiff’s own pleadings: the account was opened “to hold Bitcoin,” “to sell and reduce to dollars,” and “to trade crypto coins.” That, he said, is different from a personal checking account used for paychecks, rent, or groceries.
For Judge Liman, if the account was opened primarily for investment, it is not an EFTA “account.” The court therefore avoided the question of whether crypto itself qualifies as “funds.”
The Dissonance & Why It Matters
- Are crypto transfers “funds”?
Judge Cote in Nero emphasized that what matters is how the transfer happens—electronically—not what asset is being moved. Judge Liman in Yuille sidestepped that issue, leaving the “funds” question unresolved.
- What counts as a covered account?
Nero held that a personal account remains protected even if the user hopes to profit from it. Yuille took the opposite approach: if the account was opened primarily to invest, it falls outside EFTA’s consumer protections.
- Practical takeaway.
A consumer’s ability to invoke EFTA may turn on the story told about the account’s purpose. Was it for household or everyday use, or framed as an investment vehicle? That framing can make the difference between having federal protections—or not.
Contact Us
At Dilendorf Law Firm, we represent clients targeted by unauthorized crypto transfers and SIM-swap attacks. With more than six years of experience and over 100 consumer arbitrations, we have pursued claims against major cryptocurrency exchanges—including Coinbase—and leading carriers such as Verizon, T-Mobile, and AT&T.
Our attorneys regularly appear before AAA, JAMS, and NAM, and we also represent victims whose assets were taken from self-custody wallets (e.g., MetaMask) and other decentralized platforms. In high-stakes matters, we coordinate with U.S. law-enforcement and investigative agencies—including the FBI, Department of Homeland Security (DHS), and the Secret Service—as part of broader recovery strategies.
If you suffered losses due to a SIM-swap or a cyber fraud, contact us to discuss your case and recovery options.
Email: info@dilendorf.com | Phone: (212) 457-9797
This article is a public-record summary and does not constitute legal advice. We are not counsel of record, and the referenced cases are not affiliated with Dilendorf Law Firm.
When a Coinbase customer experiences losses after phishing, SIM-swap, or other credential compromise, several provisions in the U.S. Individual User Agreement may be relevant.
Below, we quote representative language and explain how these clauses can function in disputes.
This article is for informational purposes only and does not assert wrongdoing by any party.
This article addresses the current U.S. Individual User Agreement on Coinbase’s legal site and excerpts the precise sections Coinbase relies on in credential-theft disputes. Because Coinbase updates terms periodically, customers should always capture the agreement operative on the incident date and preserve a copy for the record.
Clause #1 — Risk of loss allocated to the customer
“Title to Supported Digital Assets shall at all times remain with you […] you shall bear all risk of loss.” (User Agreement §2.7.1, Ownership)
Because title remains with the user and the clause assigns risk of loss to the user, parties may argue that losses in an account are borne by the user absent an independent legal basis shifting or sharing that risk.
Clause #2 — Transactions using your credentials are presumed authorized
“When a […] transaction occurs using your credentials, we will assume that you authorized such transaction.” (Section 3.6)
“Reporting an unauthorized transaction does not guarantee Coinbase will be able to reverse the transaction or reimburse you for the transaction.” (Section 3.6)
In scenarios such as SIM-swap, spoofed-site, malware, or remote-access attacks, transfers signed with a user’s factors may be treated as authorized for platform purposes, and the agreement does not promise reversal or reimbursement upon later notice.
Clause #3 — No responsibility for losses from compromised credentials
“Coinbase will never […] ask you […] for your passwords, 2-factor codes, or to screen share […] Coinbase is not liable for any loss […] due to the compromise of your account login credentials.” (Section 6.7)
This clause frames losses arising from compromised login credentials (e.g., fake support calls, screen-share scams, SIM-swap, credential-stuffing) as user-side risk not attributed to Coinbase’s systems, complementing the presumption in §3.6.
Clause #4 — “AS IS” / no warranties & liability limits
“THE COINBASE SERVICES ARE PROVIDED ON AN ‘AS IS’ AND ‘AS AVAILABLE’ BASIS […].” (Section 8.2)
The agreement also includes disclaimers relating to service issues (e.g., “viruses,” “glitches, bugs, errors”) and limits certain categories of damages, subject to applicable law.
Potential effect in disputes. Even where a feature lagged or behaved unexpectedly, the no-warranty language and damages limitations may narrow contract-based recovery, subject to statutory carve-outs and jurisdiction-specific rules.
Reading the provisions together
One way to analyze these provisions is:
- Allocation: title with the user → user bears risk (Section 2.7.1)
- Authorization: activity with user credentials presumed authorized; notice alone doesn’t assure reversal (Section 3.6)
- No-fault framing: credential compromise treated as external to Coinbase (Section 6.7)
- Contract shields: “AS IS” / damages limits (Section 8.2)
Actual outcomes turn on the facts, applicable statutes, and governing law.
Case Study
Courts have addressed the enforceability of user-agreement clauses in cryptocurrency or digital-asset platforms, particularly those that allocate the risk of loss to users or include “AS IS”, no-warranty, or limitation-of-liability terms.
These cases often hinge on the interpretation of the user agreements, the presence of integration clauses, and the extent to which users are deemed to have accepted the terms.
Courts have also considered whether platforms have a legal duty beyond the terms explicitly agreed upon, especially in situations involving risks such as account compromise or loss of assets.
- In Archer v. Coinbase, Inc., 53 Cal. App. 5th 266, the court held that the cryptocurrency exchange platform was not liable for an investor’s breach of contract claim because the user agreement did not require the platform to support or provide services for a particular cryptocurrency. The agreement’s integration clause barred the use of parol evidence to impose additional obligations, and the platform had no legal duty beyond the agreed terms.
“When the parties to a written contract have agreed to it as an integration—a complete and final embodiment of the terms of an agreement—parol evidence cannot be used to add to or vary its terms.”
The court also rejected claims of conversion and negligence, emphasizing that the platform took no affirmative action to deprive the investor of the currency and had no duty to provide services beyond those agreed upon.
- In SEC v. Coinbase, Inc., 726 F. Supp. 3d 260, the court examined the risks associated with Coinbase’s staking program, noting that while users retained ownership of their crypto-assets, the assets were at risk of loss through mechanisms such as “slashing.” The user agreement limited Coinbase’s indemnification obligations, excluding losses caused by third parties, force majeure events, or other factors outside Coinbase’s control. The court highlighted that the risk of loss existed despite the absence of actual losses, and the agreement’s terms clearly allocated certain risks to the users.
“[…] once a customer’s crypto-assets are […] staked to the underlying blockchain protocol, those assets are at risk of being ‘slashed.’”
- In In re Celsius Network LLC, 649 B.R. 87, the court found that customers only had contract claims under the Terms of Use against the debtor, Celsius Network LLC, and not its affiliates.
“[…] the parties to the terms of use intended that only LLC, and not any other Debtor or non-Debtor affiliates, are liable to Customers on contract claims under the terms of use.”
The court emphasized that the Terms of Use, which customers were required to accept to access the platform, allowed the debtor to unilaterally update the terms. The updated terms defined “Celsius” to include the debtor and its affiliates, but the court determined that liability was limited to the debtor based on the terms and extrinsic evidence. The case underscores the enforceability of user agreements in defining the scope of liability and the allocation of risk.
FAQs (client-facing)
“I reported within hours—why wasn’t I reimbursed?”
Section 3.6 presumes transactions using your credentials were authorized and does not guarantee reversal or reimbursement upon notice. Whether remedies exist depends on the facts and applicable law beyond the contract.
“What if my carrier performed a SIM-swap?”
Section 6.7 states Coinbase is not liable for losses due to compromised login credentials. Any claims against other parties (e.g., a carrier) may involve different facts, evidence, and legal theories.
“What does ‘AS IS’ mean for my case?”
“No-warranty” language can narrow contract-based claims, though statutory protections (and any required carve-outs) may still apply. Outcomes turn on jurisdiction and facts.
Conclusion
The contract provisions discussed above don’t decide a case on their own—but they do set the lens. Read together, they can (i) place certain risks on the account holder, (ii) presume authorization for activity conducted with stored credentials or factors, and (iii) narrow warranty- and damages-based relief.
What actually matters is the record you build and the law that applies to it.
Contact Us
Even in difficult, credential-compromise scenarios, there are paths to evaluate and pursue.
With over six years of experience and a record of handling more than 100 consumer arbitration cases, we have pursued claims against major cryptocurrency exchanges—including Coinbase, and leading phone carriers such as Verizon, T-Mobile, and AT&T.
Our attorneys are skilled in navigating proceedings before all major arbitration forums, including AAA, JAMS, and NAM.
We also represent victims whose digital assets were stolen not only from regulated exchanges but also from self-custody wallets like MetaMask and other decentralized platforms.
If you have suffered losses due to a SIM swapping incident or other cyber fraud, contact Dilendorf Law Firm at info@dilendorf.com to discuss your case and options for recovery.
After a January 2018 SIM-swap, crypto investor Michael Terpin alleged roughly $24 million in losses and sued AT&T, arguing the carrier violated the Federal Communications Act (FCA) by permitting access to his protected customer information—customer proprietary network information (CPNI)—without proper authentication.
In 2024, the Ninth Circuit revived that FCA theory and sent the case back to the Central District of California.
On July 16, 2025, the district court partly denied AT&T’s summary-judgment motion on the FCA claim and set the case on a path toward trial, making this one of the most watched SIM-swap matters in the country.
What happened: the SIM-swap and theft
According to the record, teenager Ellis Pinsky paid Jahmil Smith, an employee at an AT&T authorized retailer, to bypass safeguards and swap Terpin’s number to a device the attackers controlled.
They then sent password-reset codes to the hijacked number, accessed Terpin’s Microsoft OneDrive, and found a .txt file in the OneDrive trash containing wallet credentials—leading to the alleged $24M loss.
As Terpin’s filing puts it, “Pinsky … bribed [Jahmil] Smith … to bypass security measures and swap Terpin’s SIM,” then used SMS resets to enter his accounts.
AT&T’s appellate brief emphasizes user-side practices: Terpin copied credentials into a separate document that synced to OneDrive; he admitted that if he hadn’t done so “he wouldn’t have suffered any crypto loss.”
Claims and legal theories
- Claims pleaded. Terpin’s operative complaint asserted fraud, negligence, contract claims, and unauthorized disclosure under the FCA (47 U.S.C. §§ 206, 222). He sought ~$24M plus punitive damages.
- Appellant’s framing. Wireless carriers control SIM swaps and must protect CPNI; a swap without proper authentication permits access to protected information and foreseeably enables downstream account takeovers.
- Defense & industry perspective. AT&T (and CTIA as amicus) argue a SIM-swap by itself does not disclose § 222-protected information and that the loss stemmed from intervening steps across third-party platforms (email, Microsoft, wallet providers). CTIA also warns that expanding § 222 could risk turning carriers into de facto insurers for cross-platform cybercrime.
Procedural history & timeline
August 15, 2018 — Filing (C.D. Cal., Los Angeles; No. 2:18-cv-06975-ODW-KS).
Terpin sues AT&T after a January 2018 SIM-swap. He alleges approximately $24 million in losses and brings fraud, negligence, contract, and FCA § 222 (CPNI) claims.
2017–2018 factual backdrop. Attackers allegedly bribed an AT&T authorized-retailer employee to perform an unauthorized SIM-swap, then used SMS password resets to access Terpin’s Microsoft OneDrive, where a .txt file in the trash contained wallet credentials—enabling the crypto theft.
September 8, 2020 — Pleadings trimmed (district court). Fraud claims and punitive-damages requests dismissed with prejudice.
March 30, 2023 — Summary judgment (district court). The court grants summary judgment to AT&T on the remaining claims, including the FCA theory. Terpin appeals.
September 30, 2024 — Ninth Circuit (No. 23-55375). Affirmed in part, reversed in part, and remanded. The panel revives only the FCA § 222 claim and instructs the district court to address proximate cause on remand.
July 16, 2025 — Order on remand (district court). On a renewed summary-judgment motion, the court grants in part / denies in part:
- A jury could find AT&T failed to take reasonable measures and properly authenticate before allowing access to CPNI during the fraudulent SIM-swap (citing 47 C.F.R. § 64.2010(a) and Global Crossing).
- AT&T prevails to the extent Terpin’s § 222 theory rests solely on the authorized-retailer employee’s (Smith’s) unauthorized acts.
What Section 222/CPNI means here
Section 222 and the FCC’s CPNI rules require carriers to safeguard customer proprietary network information and authenticate before disclosure.
On remand, the district court tied Terpin’s revived claim to these authentication and “reasonable measures” duties.
Terpin’s briefing also argues the ubiquity of SMS-based resets makes SIM-swap disclosures foreseeably harmful when a carrier permits access to a number without proper checks.
What’s next
Only one claim remains: FCA § 222 based on AT&T’s own conduct during the January 2018 swap. The court has referred the parties to a settlement conference on December 8, 2025 and set a jury trial for March 3, 2026, with pretrial on February 23, 2026.
Why this case matters beyond the parties
- SIM-swap accountability: The ruling signals that failing to authenticate before a SIM change can expose carriers to FCA liability when it “permits access” to protected information.
- Causation in cyber-heists: The Ninth Circuit’s partial revival leaves proximate cause to be hashed out on a trial record—important for future cases where telecom events trigger multi-platform compromises.
- Industry lens: CTIA warns that expansive § 222 theories could make carriers de facto insurers against downstream fraud across other services.
Contact Us
At Dilendorf Law Firm, we represent clients who have been targeted by SIM-swap attacks and other forms of cyber fraud.
With over six years of experience and a record of handling more than 100 consumer arbitration cases, we have successfully pursued claims against both major cryptocurrency exchanges—including Coinbase, Gemini—and leading phone carriers such as Verizon, T-Mobile, and AT&T.
Our attorneys are skilled in navigating proceedings before all major arbitration forums, including AAA, JAMS, and NAM.
We also represent victims whose digital assets were stolen not only from regulated exchanges but also from self-custody wallets like MetaMask and other decentralized platforms.
In high-stakes cases, we advise and coordinate with U.S. law enforcement and investigative agencies—including the FBI, Department of Homeland Security (DHS), and the Secret Service—as part of broader recovery strategies and criminal investigations into cybercrime.
If you have suffered losses due to a SIM swapping incident or other cyber fraud, contact us to discuss your case and options for recovery.
Email: info@dilendorf.com | Phone: 212.457.9797
Disclaimer: This summary is based on public records and does not constitute legal advice. Dilendorf Law Firm is not counsel of record for Michael Terpin, and his case is in no way affiliated with our firm.

