Who Owns the Merchant Portfolio? The Contract Decides
In the payment processing industry, merchant portfolios are the core economic asset of an Independent Sales Organization (ISO). They generate residual income, determine exit valuations, and form the foundation of business leverage.
Yet in disputes between ISOs, sub-ISOs, processors, and acquiring banks, one recurring question dominates:
Who actually owns the merchant portfolio?
Federal and state courts consistently provide the same answer:
Ownership, vesting, transfer rights, and residual control are determined by the contract — and courts enforce it strictly.
This article examines how courts analyze merchant portfolio ownership under ISO agreements, focusing on:
- Ownership triggers and vesting
- Transfer restrictions
- Post-termination residual rights
- Conditions precedent
- Survival clauses
- Ambiguity and course of performance
-
Ownership and Vesting: The Contract Controls
The leading appellate decision addressing merchant portfolio ownership is:
Process America, Inc. v. Cynergy Holdings, LLC, 839 F.3d 125 (2d Cir. 2016)
In Process America, the ISO argued that its portfolio ownership vested once it met contractual benchmarks. The agreement defined an “Ownership Trigger Date,” after which ownership would shift.
However, the Second Circuit emphasized that even after the trigger date, the ISO could not freely transfer the merchant agreements. Section 2.6.B imposed strict conditions, including:
- Granting the processor a right of first refusal
- Paying an exit fee
- Executing a new processing agreement acceptable to the processor and bank
The court enforced these conditions as written.
Key takeaway: “Ownership” language in ISO agreements does not necessarily mean unrestricted control. Vesting may be conditional and subject to compliance with multiple contractual prerequisites.
-
Transfer Rights and Restrictions Are Enforceable
In Process America, the ISO solicited merchants and transferred portions of the portfolio without complying with Section 2.6.B. The court found this conduct violated the agreement and caused damages due to merchant attrition.
Courts treat ISO agreements as sophisticated commercial contracts. If the agreement imposes:
- A right of first refusal
- Exit fees
- Consent requirements
- Replacement processing agreements
those restrictions will be enforced.
An ISO cannot circumvent transfer conditions simply because it sourced the merchant relationship.
-
Post-Termination Control and Reserve Funds
Portfolio disputes often arise after termination.
In the related bankruptcy proceeding In re Process America, Inc., 588 B.R. 82 (Bankr. E.D.N.Y. 2018), the court held that the processor was not obligated to release reserve funds until merchant agreements were terminated pursuant to the contract.
Post-termination rights — including reserves and residuals — are governed strictly by the agreement’s language. Courts do not imply broader rights beyond the text.
-
Residual Rights After Termination
Residual income survival is frequently misunderstood.
In Universal Bankcard Systems, Inc. v. Bankcard America, Inc., 998 F. Supp. 961 (N.D. Ill. 1998) the sub-ISO agreement provided that Universal was entitled:
“[…] to receive residuals over the lifetime of its accounts as long as the ISO services the account, […] whether or not this Agreement has been terminated.”
However, the same agreement gave the lead ISO the right:
“[…] sell, at its sole discretion, any portion or all of its merchant base, and in said event, upon the completion of said sale to a bona fide third party, the right of [Universal] to receive residuals arising from said accounts shall cease.”
This dual structure illustrates a critical principle:
Lifetime residual language can be contractually limited by a sale-of-portfolio clause.
Even strong residual survival provisions may be extinguished upon a qualifying sale.
-
The ISO’s Role in Merchant Relationships
Courts also analyze how ISO agreements fit within the broader processing structure.
In Spread Enterprises, Inc. v. First Data Merchant Services Corp., 298 F.R.D. 54 (E.D.N.Y. 2014) the court described the contractual architecture between merchants and processors:
Processors “[…] enter into contracts with different Merchants by which [they agree] to perform several processing functions for the Merchant, such as the authorization, batching, clearing and settlement functions of a credit card transaction.”
Merchant agreements are often:
- Between merchant and acquiring bank
- Sponsored by a processor
- Serviced by an ISO
Thus, an ISO’s “ownership” may refer only to economic rights — not legal ownership of the merchant contract itself.
-
When Do Residual Rights Actually Vest?
Courts distinguish between:
- Accrued rights
- Conditional rights
- Contingent rights
Under federal law, a right is considered vested when it is unconditional and immediately claimable. See Romines v. Great-West Life Assurance Co., 73 F.3d 1457 (8th Cir. 1996).
In the payment processing context, courts routinely examine whether contractual conditions precedent were satisfied before termination.
In Lawson v. Heartland Payment Systems, LLC, 548 F. Supp. 3d 1085 (D. Colo. 2020) the court addressed commission and residual claims in the processing industry employment context.
The court emphasized that compensation rights depend on satisfaction of contractual conditions. If installation, execution, or servicing requirements are not complete at termination, commissions may not vest.
Vesting depends on performance of contractual conditions — not expectations.
-
Conditions Precedent and Contractual Precision
Several courts have refused to recognize vesting where required steps were not completed.
If an ISO agreement ties residual rights to:
- Executed merchant contracts
- Approved applications
- Installed terminals
- Active servicing
then those elements must be satisfied before vesting occurs.
Absent fulfillment of conditions precedent, residual claims may fail.
-
Ambiguity and Course of Performance
When contractual language is ambiguous, courts may examine extrinsic evidence.
For example, in Orkin v. Albert, 162 F.4th 1 (2025), the court relied on the parties’ conduct — including forwarding of residual payments — to interpret ownership intent.
However, where the language is clear, courts will enforce the agreement as written, even if the result appears harsh.
Conclusion: Portfolio Ownership Is a Contractual Allocation of Risk
The consistent judicial theme across Process America, Universal Bankcard, Spread Enterprises, and related decisions is unmistakable:
Ownership, vesting, transfer rights, and residual survival depend entirely on the contractual structure.
An ISO may believe it “owns” its portfolio. But unless the contract supports that belief — and all conditions are satisfied — courts will enforce the agreement as written.
Merchant portfolio disputes are not emotional disputes about business relationships.
They are contractual disputes governed by precise drafting.
Contact Us
If you are negotiating an ISO agreement, facing a residual termination dispute, or evaluating a portfolio transfer or sale, strategic legal analysis is essential.
Contact Dilendorf Law Firm at info@dilendorf.com to schedule a confidential consultation.
If you sent crypto on the wrong network to a U.S. exchange, Dilendorf Law Firm can help. The firm focuses on crypto disputes and arbitration for U.S. customers.
How U.S. exchanges treat wrong‑network deposits
U.S. exchanges try to put all “wrong network” risk on you. Their user agreements and help pages say that unsupported or mis‑sent deposits are your problem, not theirs.
Support teams quote this language when they tell you your funds are “lost” or “irrecoverable.”
Coinbase (U.S.): “not liable” for unsupported assets
Coinbase’s U.S. User Agreement warns that you may use your wallet only for “Supported Digital Assets.”
-
“Your Digital Asset Wallet is intended solely for proper use of Supported Digital Assets as designated on the Coinbase Site.”
-
“Under no circumstances should you attempt to use your Digital Asset Wallet to store, send, request, or receive any assets other than Supported Digital Assets. Coinbase assumes no responsibility in connection with any attempt to use your Digital Asset Wallet with Digital Assets that we do not support.”
-
“You acknowledge and agree that Coinbase is not liable for any unsupported Digital Asset that is sent to a wallet associated with your Coinbase Account.”
If you send crypto over an unsupported network, Coinbase points to this language. It tells users that such assets “may be permanently lost” and that it “cannot recover these assets or funds.”
Coinbase sometimes offers “asset recovery” tools. But those are discretionary. The contract is written so Coinbase can say it does not owe you a duty to recover.
Binance.US: “unable to recover/return” unsupported deposits
Binance.US uses similar wording. Its help center is blunt about wrong‑network deposits.
-
“Binance.US is unable to recover/return deposits of unsupported assets or deposits sent using unsupported networks.”
-
It notes that sending to the wrong network “often lead[s] to irrecoverable funds.”
-
Another page adds: “Binance.US is not liable for any losses if you deposit an unsupported asset, deposit assets using an unsupported network, or transfer an asset to an address not owned by Binance.US.”
Binance.US has a “Deposit Recovery Tool” for some cases. But it excludes unsupported assets and unsupported networks.
Uphold: refusing to retrieve funds on unsupported networks
Uphold takes the same position. In complaints involving wrong‑network transfers, Uphold admits the funds are at a wallet linked to your account but still refuses to act.
In one BBB response, Uphold wrote:
-
“Although the transaction appears on the blockchain at an address associated with your Uphold account, our platform infrastructure does not support access to assets on unsupported networks.”
-
“While we sympathize with the situation and understand that mistakes can happen, we regret to inform you that we are unable to retrieve or return funds sent via unsupported networks at this time.”
Users report the same outcome. If the asset or network is “unsupported,” Uphold tells them: “we cannot recover them. They’re gone!”
What this means for U.S. victims
The pattern is clear:
-
Exchanges define what is “supported.” They can change this at any time.
-
If you send crypto on an unsupported network, they say they are “not liable” and “unable to recover/return” your funds.
-
They use this language to close your ticket, even when blockchain data shows the funds in an exchange‑controlled wallet.
Many victims stop there. They assume there are no options.
How Dilendorf Law Firm helps
Max Dilendorf and Dilendorf Law Firm focus on exactly these kinds of disputes. The firm has handled more than 130 cybercrime and crypto‑related arbitrations against exchanges and telecom carriers in U.S. forums such as AAA, JAMS, and NAM.
Here is how the firm approaches wrong‑network cases:
-
Read the contract. The team analyzes the U.S. user agreement, risk disclosures, and arbitration clause that applied to your account and date of loss.
-
Trace the funds. Using blockchain tools, they show your funds reached an address controlled by the exchange.
-
Attack one‑sided terms. In arbitration, they argue that boilerplate “not liable” language cannot excuse an exchange when its own design, warnings, or support behavior helped cause the loss.
-
Run the arbitration. They draft the demand, handle discovery, work with experts, and present your case at the hearing. They have already done this in 130+ cyber and crypto matters.
This is core work for the firm, not a side project.
When to contact Dilendorf Law Firm
Consider contacting Dilendorf Law Firm if:
-
You are a U.S. customer.
-
You sent BTC, ETH, USDT, USDC, or another asset to Coinbase, Binance.US, Uphold, or another U.S. platform on the wrong network.
-
Support pointed you to language like “not liable for any unsupported Digital Asset” or “unable to recover/return deposits of unsupported assets or deposits sent using unsupported networks.”
The firm can review your transaction, explain the terms that exchanges rely on, and outline arbitration or other strategies.
With experience in more than 130 crypto and cybercrime arbitrations, Dilendorf Law Firm is well‑positioned to challenge “lost forever” responses and pursue recovery of wrong‑network deposits
Venue provisions in an ISO agreement are not secondary terms. They determine where and how disputes over residual payouts, portfolio ownership, termination, rights of first refusal, or indemnification will be resolved.
The choice between federal court, state court, and arbitration can materially affect cost, timing, leverage, and outcome.
For ISOs, venue is a strategic business decision—not merely a procedural clause.
Arbitration: The Dominant ISO Model
Most modern ISO agreements require mandatory arbitration, typically administered by:
- AAA (American Arbitration Association)
- JAMS
- NAM (National Arbitration and Mediation)
Arbitration clauses are strongly favored under the Federal Arbitration Act (FAA).
In Henry Schein, Inc. v. Archer & White Sales, Inc., 586 U.S. 63 (2019), the Supreme Court made clear:
“Under the Federal Arbitration Act (FAA), arbitration is a matter of contract, and courts must enforce arbitration contracts according to their terms.”
The Court further emphasized:
“The Federal Arbitration Act does not contain a ‘wholly groundless’ exception, and courts are not at liberty to rewrite the statute passed by Congress and signed by the President.”
Similarly, in AT&T Mobility LLC v. Concepcion, 563 U.S. 333 (2011), the Court reinforced the federal policy favoring arbitration and the principle that arbitration agreements must be enforced as written.
The practical takeaway for ISOs is straightforward: arbitration clauses—including venue designations, delegation provisions, and class-action waivers—are rarely invalidated.
Venue Under the FAA
The FAA also governs arbitration-related venue mechanics.
In Cortez Byrd Chips v. Bill Harbert Constr. Co., 529 U.S. 193 (2000), the Supreme Court held that the FAA’s venue provisions in §§ 9–11 are permissive rather than restrictive, meaning courts may confirm or vacate arbitration awards in more than one permissible venue.
However, compelling arbitration under 9 U.S.C. § 4 is treated differently. Federal courts have recognized that § 4 contains mandatory language requiring arbitration to proceed within the district where the petition to compel is filed.
These distinctions matter when drafting arbitration and venue language in ISO agreements.
Federal and State Court Litigation
If an ISO agreement designates litigation rather than arbitration, forum-selection clauses are also strongly enforced.
In The Bremen v. Zapata Off-Shore Co., 407 U.S. 1 (1972), the Supreme Court held:
“Forum-selection clauses are prima facie valid and should be enforced unless enforcement is shown by the resisting party to be unreasonable under the circumstances.”
The Court further explained:
“Where the choice of a forum was made in an arm’s-length negotiation by experienced and sophisticated businessmen, absent some compelling and countervailing reason, it should be honored by the parties and enforced by the courts.”
In other words, once a venue clause is agreed upon, courts will rarely disturb it.
Why ISOs Often Choose Arbitration
ISOs frequently accept arbitration because it offers:
- Faster resolution
- Confidential proceedings
- Streamlined procedures
- Decision-makers with commercial expertise
Confidentiality alone can be critical in disputes involving residual streams, merchant portfolios, or termination rights.
The Cost Reality
Arbitration is often faster—but not necessarily cheaper.
Unlike courts, arbitration requires:
- Administrative filing fees
- Arbitrator hourly compensation
- Institutional fees (AAA, JAMS, NAM)
- Hearing logistics and scheduling costs
In complex ISO disputes—particularly those involving forensic accounting, portfolio valuation, or multi-year residual calculations—arbitration costs can exceed federal court litigation.
Additionally, arbitration awards are subject to extremely limited judicial review. Errors of law are rarely grounds for reversal.
Arbitration and Venue: Strategic Review Before Signing
An arbitration clause should be reviewed carefully before signing an ISO agreement. ISOs should confirm:
- Which organization will administer the arbitration (AAA, JAMS, or NAM);
- Where the arbitration will take place;
- Whether the case will be decided by a single arbitrator or a panel;
- How arbitration fees and attorneys’ fees are allocated;
- How broadly the clause is drafted;
- Whether any claims are carved out for court relief.
Language covering disputes “arising out of or relating to” the agreement may capture nearly all claims, including termination, indemnification, rights of first refusal, liability caps, and residual calculations.
Because courts “must enforce arbitration contracts according to their terms,” and forum-selection clauses are “prima facie valid,” venue provisions are rarely negotiable after a dispute arises.
A mandatory arbitration clause combined with fee-shifting may increase financial exposure. Conversely, a carefully negotiated clause can preserve leverage in a dispute with a payment processor or sponsoring bank.
Venue is not merely procedural—it is strategic.
Protect Your Position Before You Sign
At Dilendorf Law Firm, we represent ISOs and payment industry participants in negotiating ISO agreements, including arbitration clauses, venue provisions, residual payout protections, rights of first refusal, and risk allocation mechanisms.
If you are negotiating an ISO agreement—or facing a dispute with a payment processor or sponsoring bank—contact us at info@dilendorf.com to protect your residual income, portfolio rights, and strategic position.
When a victim’s phone is stolen and cryptocurrency is drained from an exchange account, exchanges and telecommunications carriers often argue that the loss was caused solely by third-party criminals.
Dilendorf Law Firm represents victims whose phones were stolen and thieves initiated unauthorized activity from the victims’ cryptocurrency exchange accounts.
The firm handles disputes involving account takeovers, SIM-swap attacks, and rapid unauthorized withdrawals.
Courts do not automatically accept the “third-party criminal” defense.
Courts examine if an exchange’s own security systems, authentication controls, monitoring procedures, or response measures contributed to the loss.
These cases are highly fact-intensive and high risk. Most exchanges require arbitration.
They assert broad contractual defenses.
Duty to Implement Adequate Security Measures
In Yuille v Uphold HQ Inc., 686 F Supp 3d 323, 335-336 (S.D.N.Y. 2023), the court summarized allegations that the exchange failed to safeguard customer accounts. The complaint alleged that Uphold failed to provide adequate security by:
“failing to provide reasonable and appropriate security to prevent unauthorized access to its customer’s account … misrepresenting ‘the safety and security of’ its accounts … failing ‘to adequately safeguard and protect’ the accounts; [and] failing ‘to use readily available security measures to prevent or limit unauthorized access to customer accounts and to prevent unauthorized transactions from occurring on those accounts.’”
The case reflects that exchanges may face liability where internal controls are insufficient to prevent foreseeable unauthorized access.
In Rider v Uphold HQ Inc., 657 F Supp 3d 491, 496 (S.D.N.Y. 2023), the plaintiffs challenged the exchange’s authentication architecture.
The court described allegations that Uphold’s implementation of two-factor authentication allowed unauthorized users to access accounts without the original device, thereby compromising account security.
In a stolen-phone case, these allegations are critical.
If authentication can be bypassed without meaningful device verification, biometric confirmation, or withdrawal delays, plaintiffs could argue that the exchange’s security design contributed to the loss.
Negligence and Weakened Safeguards
In Yuille, the court also described allegations that user-experience changes weakened security protections.
The complaint alleged that measures adopted to improve customer service:
“weakened its account security by reducing the situations in which Uphold would restrict [unauthorized] account access.”
Negligence claims often focus on operational failures.
These may include failing to suspend credentials after repeated failed login attempts, failing to delay withdrawals after password resets, or failing to flag large transfers to newly added wallets.
If safeguards are relaxed for convenience, plaintiffs may argue that reasonable care was not exercised.
Misrepresentation of Security Standards
Exchanges frequently advertise strong protections. In Pillar Project AG v Payward Ventures, Inc., 64 Cal App 5th 671, 674, 279 Cal Rptr 3d 117, 121 (2021), the court described allegations that the exchange:
“…falsely advertised that it provided the best security in the business.”
and that those measures were
“...failed to use standard security measures on its exchange which would have prevented the theft.”
If an exchange promotes “bank-level security” or “advanced fraud monitoring,” yet fails to stop rapid unauthorized withdrawals after a phone theft or SIM-swap attack, those statements may support misrepresentation claims.
Role of Telecommunications Carriers
Stolen-phone and SIM-swap cases often involve telecommunications carriers.
Major carriers such as Verizon, AT&T, and T-Mobile may be implicated where unauthorized SIM swaps or account changes enabled access to exchange accounts.
If a carrier transfers a number without proper identity verification, disables PIN protections, or fails to detect suspicious account activity, plaintiffs may assert negligence or statutory claims against the carrier.
Liability analysis often requires examining both the exchange’s authentication systems and the carrier’s account-security procedures.
Arbitration and High-Risk Litigation
These cases are high risk. Major exchanges, including Coinbase, Binance, Gemini, and Uphold, require arbitration.
They assert assumption-of-risk defenses and argue that possession of login credentials constitutes authorization.
They also argue that third-party criminal acts break the chain of causation.
Carriers raise contractual limitations and federal preemption defenses. Success depends on forensic evidence.
This includes IP logs, device fingerprints, authentication records, internal security policies, SIM-swap documentation, and timing of notice.
Dilendorf Law Firm’s Experience
Dilendorf Law Firm represents victims in stolen-phone and SIM-swap cases involving unauthorized cryptocurrency transfers.
The firm represents clients in disputes against Coinbase, Binance, Gemini, Uphold, and other exchanges.
The firm also represents clients in cases against Verizon, AT&T, T-Mobile, and other telecommunications carriers.
To date, the firm has arbitrated more than 130 cases against crypto exchanges and phone carriers.
These matters involve complex arbitration clauses, evolving regulatory standards, and sophisticated technical evidence.
Stolen-phone cryptocurrency disputes are not routine consumer claims.
They are high-risk, high-stakes proceedings that require experienced arbitration counsel and detailed forensic investigation.
Conclusion
Cases such as Yuille, Rider, Pillar Project, and Widjaja show that exchanges and financial institutions are not automatically insulated from responsibility when unauthorized transfers follow a phone theft.
Plaintiffs may establish liability by demonstrating inadequate safeguards, weakened controls, misleading security representations, or failure to act promptly after notice. Carrier conduct may also be central to the analysis.
At the same time, these cases are complex, arbitration-driven, and high risk.
Careful evaluation of contracts, regulatory obligations, and technical evidence is essential before proceeding.
Contact Us
If your phone was stolen and thieves transferred cryptocurrency or funds out of your exchange account without your authorization, contact Max Dilendorf at Dilendorf Law Firm.
Email: max@dilendorf.com
Phone: 212.457.9797
Early action is critical in stolen-phone and unauthorized crypto transfer cases. Prompt investigation can help preserve evidence and assess potential claims against exchanges and telecommunications carriers.
Domestic Asset Protection Trusts (DAPTs) are often discussed as sophisticated tools for shielding assets from future creditor claims.
When designed correctly—and, critically, implemented before legal trouble arises—DAPTs can play a legitimate role in long-term wealth and risk planning. But courts have been equally clear that DAPTs are not retroactive shields and do not override fraudulent transfer law.
The Alaska Supreme Court’s decision in Toni 1 Trust v. Wacker is a clear and instructive example of where a DAPT failed to protect assets, not because the trust statute was invalid, but because the planning collided with creditor-rights principles and jurisdictional limits.
Background: Judgments First, Trust Funding Second
The case arose after courts in Montana entered a series of judgments in 2011 and 2012 against Donald Tangwall and members of his family. Only after those judgments were entered, two parcels of real property transferred into a trust known as the Toni 1 Trust.
As the Alaska Supreme Court summarized the sequence of events:
“After a Montana state court issued a series of judgments against Donald Tangwall and his family, the family members transferred two pieces of property to the ‘Toni 1 Trust’[…]”
The trust was described as “a trust allegedly created under Alaska law,” placing it squarely within Alaska’s statutory framework for self-settled asset protection trusts.
Creditors did not challenge the trust in the abstract. Instead, they challenged the transfers themselves, arguing that the conveyances were made to avoid satisfaction of the Montana judgments. Both a Montana state court and a federal bankruptcy court agreed, concluding that:
“[…] the transfers were made to avoid the judgments and were therefore fraudulent.”
Those rulings became the foundation for the later Alaska litigation.
The Trustee’s Alaska Strategy
Rather than attacking the fraudulent transfer findings on their merits, the trustee pursued a jurisdictional strategy. Relying on Alaska Statute § 34.40.110(k), the trustee argued that only Alaska courts had subject-matter jurisdiction to decide whether transfers into an Alaska DAPT were fraudulent.
As the Alaska Supreme Court framed the argument:
“Tangwall, the trustee of the Trust, then filed this suit, arguing that Alaska state courts have exclusive jurisdiction over such fraudulent transfer actions under AS 34.40.110(k).”
If accepted, this position would have rendered the Montana and federal bankruptcy court decisions void for lack of jurisdiction—effectively using Alaska’s DAPT statute as a jurisdictional shield.
Why the Alaska Supreme Court Rejected That Argument
The Alaska Supreme Court rejected the trustee’s position decisively, grounding its analysis in long-standing principles of interstate and federal jurisdiction.
First, the Court made clear that a state legislature cannot unilaterally strip other courts of jurisdiction:
“This statute cannot unilaterally deprive other state and federal courts of jurisdiction.”
The Court emphasized that jurisdiction is determined by the law of the forum hearing the case, not by another state’s attempt to reserve disputes for itself:
“Jurisdiction is to be determined by the law of the court’s creation, and cannot be defeated by the extraterritorial operation of a statute of another state.”
This point is especially important in the DAPT context. Fraudulent transfer claims are considered transitory actions, meaning they may be brought wherever a court has personal jurisdiction over the parties. Alaska could not convert those claims into Alaska-only proceedings by statute.
Federal Bankruptcy Jurisdiction Cannot Be Curtailed
The Alaska Supreme Court also addressed the limits of state power vis-à-vis federal courts. Because the fraudulent transfer findings were also made in a federal bankruptcy proceeding, the trustee’s argument necessarily required Alaska law to override federal jurisdiction.
The Court rejected that premise outright, explaining that states have:
“[…] no power to enlarge or contract the federal jurisdiction.”
Federal bankruptcy courts derive their authority from federal law, including express statutory powers to avoid fraudulent transfers. State DAPT statutes cannot negate or restrict those powers.
The Result: No Jurisdictional Shield, No Asset Protection
Having rejected the trustee’s jurisdictional arguments, the Alaska Supreme Court affirmed dismissal of the Alaska action in full:
“We therefore affirm the superior court’s judgment dismissing Tangwall’s complaint.”
The practical consequence was straightforward: the Toni 1 Trust did not succeed in insulating the transferred assets from creditor claims, and the prior fraudulent transfer rulings remained effective.
What Toni 1 Trust v. Wacker Does—and Does Not—Stand For
This case is sometimes mischaracterized as a rejection of DAPTs generally. That is not what the Alaska Supreme Court held.
Instead, the decision reinforces several well-established principles:
- DAPTs do not override fraudulent transfer law.
If assets are transferred after judgments are entered—or when creditor claims are reasonably foreseeable—those transfers remain vulnerable. - Timing matters as much as structure.
Asset protection planning must be done before legal trouble arises, not in response to it. - Jurisdictional provisions have limits.
No state can force other states or federal courts to surrender jurisdiction over creditor-rights claims. - DAPTs are planning tools, not emergency measures.
Courts will distinguish between legitimate long-term planning and efforts to place assets beyond reach after liability has attached.
How This Case Fits into Broader Asset Protection Planning
When viewed alongside cases like In the Matter of the CES 2007 Trust, Toni 1 Trust v. Wacker provides an important counterbalance.
One shows how asset protection structures can be respected when properly implemented; the other shows what happens when planning is attempted too late.
For clients—U.S. and non-U.S. alike—the lesson is consistent: effective asset protection requires early planning, careful jurisdictional analysis, and compliance with fraudulent transfer law.
Conclusion
Toni 1 Trust v. Wacker underscores a simple but critical truth: a Domestic Asset Protection Trust is not a cure for existing legal problems. Courts will look beyond statutory labels to timing, intent, and substance.
For those considering DAPT planning, the decision serves as a cautionary example—and a reminder that thoughtful, proactive planning is essential.
Contact Us
At Dilendorf Law Firm, we assist U.S. and international clients with sophisticated cross-border estate and asset protection planning. Our practice spans domestic asset protection trusts (DAPTs) in leading U.S. jurisdictions—such as Wyoming, Alaska, Nevada, and South Dakota—as well as offshore trust structures in key jurisdictions including the Cook Islands, Nevis, and the Cayman Islands.
In each jurisdiction, we have developed a network of experienced trustees, financial institutions, and vetted legal partners who help ensure that every structure is professionally administered and compliant with local regulatory standards.
To discuss how our experience and network can support your planning goals, contact us at info@dilendorf.com or by calling us at 212.457.9797 to discuss your needs.
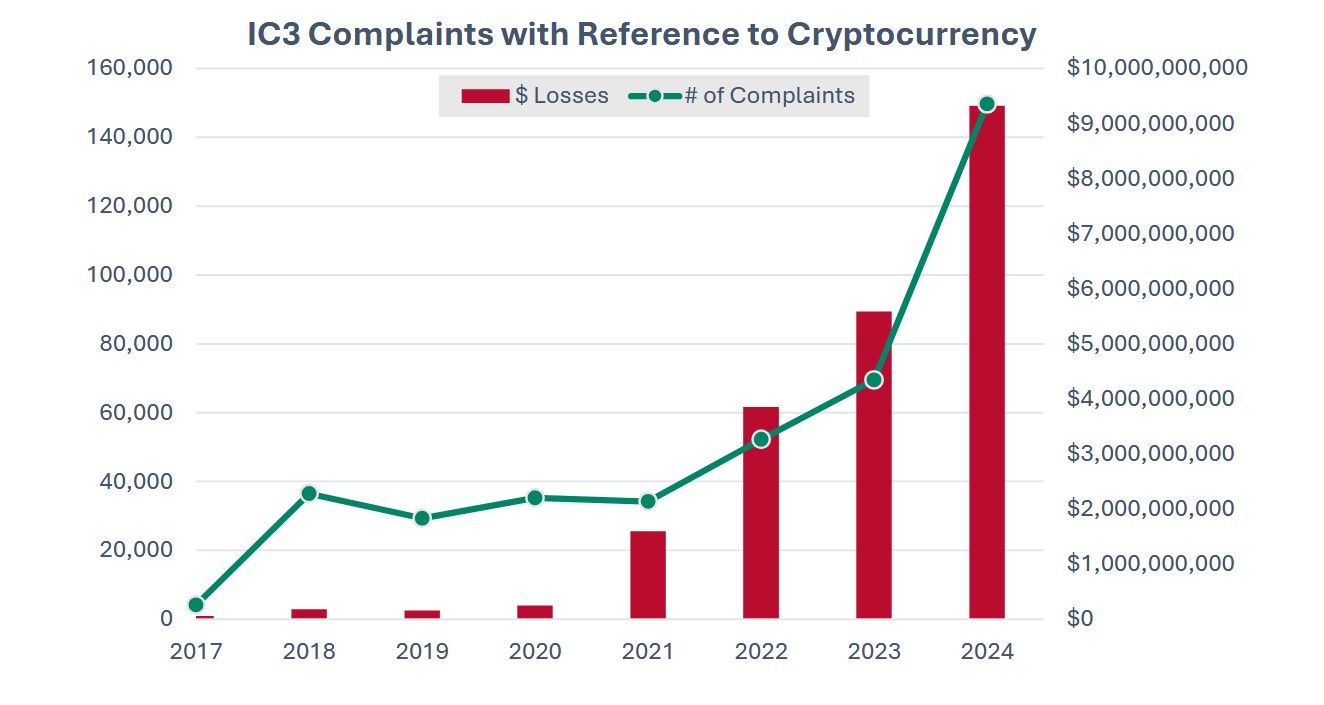
SIM Swap Attacks in 2026: What Victims Need to Know
If you believe you were the victim of a SIM swap attack and lost cryptocurrency or access to your accounts, start with the video above. It explains what likely happened and what legal options may be available.
SIM swap attacks are rapidly increasing in 2026. They are now one of the most damaging forms of cybercrime affecting crypto holders, investors, and everyday consumers.
These attacks often begin when a mobile carrier transfers a customer’s phone number to a SIM card controlled by a criminal.
Once that happens, the attacker receives your calls, text messages, and security codes.
They can reset passwords and access email accounts, crypto exchanges, and self-custody wallets. In many cases, cryptocurrency and other assets are stolen within minutes.
Victims often realize what happened only after their phone stops working.
Many people searching for a SIM swap attorney or SIM swap lawyer are surprised to learn how complex these cases can be.
SIM swap attacks frequently involve failures by wireless carriers such as T-Mobile, Verizon, AT&T, or other providers.
These failures may include weak authentication procedures, ignored security flags, or unauthorized SIM transfers.
When carrier security failures lead to stolen cryptocurrency or financial losses, victims may have legal claims.
These claims are often pursued through arbitration or litigation under federal telecommunications law and consumer protection rules. Timing matters. Evidence can disappear quickly, and deadlines may apply.
In the video above, Max Dilendorf, founder of Dilendorf Law Firm, explains how SIM swap attacks work.
He also discusses why these crimes are accelerating in 2026 and what victims should do immediately after discovering an attack.
Dilendorf Law Firm has handled more than 130 cybercrime and crypto-related matters. These include SIM swap attacks, cryptocurrency theft, software liability disputes, and AI-related fraud.
The firm regularly represents victims in complex arbitration cases against major mobile carriers.
This video is designed to help victims understand their rights. It explains why acting quickly is critical. It also outlines how working with an experienced SIM swap lawyer can help victims evaluate potential recovery options.
Resources:
- Cryptocurrency – Internet Crime Complaint Center (IC3)
- NYDF Consumer Complaint
- AAA Consumer Arbitration Rules
- JAMS Comprehensive Arbitration Rules & Procedures
- Crypto Enforcement
- Modern Scams: How Scammers are Using Artificial Intelligence and How We Can Fight Back
- Cryptocurrency Fraud Report 2023
- Cryptocurrency: Selected Policy Issues
- Combatting Illicit Activity Utilizing Financial Technologies and Cryptocurrencies
- Crypto-Assets: Implications for Consumers, Investors, and Businesses
- Exploring the Cryptocurrency and Blockchain Ecosystem
- Crypto Assets
- What To Know About Cryptocurrency and Scams
- Digital Assets | CFTC
- Taxpayers need to report crypto, other digital asset transactions on their tax return
Crypto Stolen from Coinbase or Another Exchange? Dilendorf Law Can Help
If your cryptocurrency was stolen from Coinbase or another U.S.-based crypto exchange and the platform denied responsibility, you may still have legal options.
Many victims are told there is nothing an exchange can do—but that is often not the end of the story.
In this video, Max Dilendorf, a New York–based crypto attorney, explains how exchange User Agreements and mandatory arbitration clauses can provide a legal path forward for recovering stolen crypto.
👉 Watch the full video on YouTube:
What This Video Is About
This video focuses on one of the most misunderstood—but most important—documents in crypto disputes: the User Agreement you accepted when opening your exchange account.
Since 2017, Dilendorf Law has worked exclusively in the crypto space.
Since 2019, the firm has been among the first in the U.S. to represent victims of exchange-related crypto theft in arbitration and litigation. To date, the firm has handled 130+ arbitration cases involving stolen customer funds.
In this episode, Max explains:
-
Why exchanges rely on User Agreements to deny liability
-
How arbitration clauses often replace lawsuits as the only legal remedy
-
Why these agreements are legally enforceable—even if you never read them
-
How missing a notice or procedural step can permanently block your claim
Key Topics Covered in the Video
1. Reviewing the Exchange User Agreement
If an exchange refuses to reimburse stolen funds, the User Agreement becomes the legal roadmap for your claim. Max explains how to locate and analyze the dispute resolution and arbitration sections.
2. Understanding Mandatory Arbitration
Most U.S. crypto exchanges require disputes to be resolved through private arbitration—not court. The video explains how arbitration works, why it is binding, and what limitations apply.
3. Notice Requirements Before Arbitration
Many exchanges require victims to send a formal written notice before filing arbitration. The video explains common deadlines (30–60 days), delivery methods, and why failing to comply can derail a case.
4. Choosing the Arbitration Forum
The video breaks down the most common arbitration providers used by crypto exchanges:
-
American Arbitration Association (AAA)
-
JAMS
-
National Arbitration and Mediation (NAM)
Each forum has different rules, fees, and procedures—experience matters.
5. Why Legal Strategy Matters
Arbitration decisions are usually final, with limited appeal rights. Max explains why preparation, proper filing, and legal strategy significantly affect outcomes in stolen-crypto cases.
Who Should Watch This Video
This video is especially relevant if:
-
Your Coinbase or exchange account was hacked
-
You experienced unauthorized withdrawals or transfers
-
The exchange denied reimbursement or blamed the user
-
You’re unsure how arbitration works or where to start
Need Legal Help After Crypto Theft?
If your crypto was stolen and the exchange refused to help, you may still have options—but timing and procedure are critical.
Contact Dilendorf Law:
📧 info@dilendorf.com
📞 212-457-9797
This video is for educational purposes only and does not constitute legal advice. For guidance specific to your situation, consult a qualified crypto attorney.
U.S. & International Asset Protection and Estate Planning for High-Risk Professionals and Global Entrepreneurs
In this video, Max Dilendorf, founder of Dilendorf Law Firm, explains how individuals and business owners can protect assets in an increasingly aggressive legal and regulatory environment through sophisticated U.S. and international planning strategies.
Dilendorf Law Firm represents U.S. and non-U.S. clients worldwide, including doctors, surgeons, physicians, entrepreneurs, real estate developers, architects, and other high-risk professionals who require advanced asset protection and long-term wealth preservation.
We also advise international clients moving businesses or investments to the United States, providing cross-border tax planning, tax structuring, and U.S. business formation services.
The video discusses both onshore and offshore asset protection solutions, including:
-
U.S. asset protection trusts and dynasty trusts in favorable jurisdictions such as Alaska, Wyoming, Delaware, and South Dakota
-
Offshore trust and holding structures in jurisdictions including the Cayman Islands, Cook Islands, Switzerland, Liechtenstein, Nevis, and the United Arab Emirates
-
Integrated estate planning for families with U.S. and international assets
-
Compliant planning for U.S. and foreign real estate ownership
Max also addresses the firm’s extensive experience in crypto law and digital asset protection, including secure custody strategies and crypto-related litigation, and how digital assets can be incorporated into a broader asset protection and estate planning framework.
Whether you are a U.S. professional seeking protection from litigation risk, or an international business owner navigating U.S. tax and compliance rules, this video outlines how a carefully structured, fully compliant global “Plan B” can help safeguard wealth across borders.
Contact Us
If you are considering U.S. or international asset protection, estate planning, or cross-border business structuring, contact Dilendorf Law Firm for a confidential consultation.
Email: info@dilendorf.com | Phone: 212.457.9797
Our team works with clients in the United States and internationally to develop compliant, strategic solutions tailored to complex risk profiles and global assets.
On December 17, 2025, Coinbase introduced an updated version of its User Agreement.
While many users expected major changes to arbitration and dispute‑resolution rules, those provisions were not amended and continue to govern how hacked‑account and stolen‑funds disputes must be resolved in 2026.
For victims whose crypto was stolen from Coinbase, understanding how these terms allocate risk, limit liability, and channel claims into arbitration is critical to planning an effective recovery strategy.
New Services, Same Arbitration Framework
The update primarily adds and clarifies new services rather than changing the core dispute‑resolution mechanics.
-
Coinbase introduced a Token Sale Platform that lets users purchase newly issued digital assets directly from third‑party developers, with Coinbase acting only as a platform provider.
-
The agreement clarifies that U.S. equities trading is conducted through Coinbase Capital Markets Corporation, a registered broker‑dealer affiliate that is legally separate from Coinbase’s digital asset services.
Even with these additions, the mandatory arbitration provisions and class‑action waiver that apply to most crypto‑related disputes remain in place.
Limitation of Liability
The User Agreement continues to impose significant limitations on Coinbase’s liability.
In most circumstances, a user’s potential recovery is capped at the value of the supported digital assets held in the user’s wallet at the time the claim arises.
Users also generally waive the right to recover lost profits, loss of business opportunities, diminution in value, data loss, or other indirect or consequential damages.
Coinbase also provides its services on an “as is” and “as available” basis, disclaims most warranties, and does not guarantee that transactions will be executed accurately or at all.
Liability beyond these limits is permitted only if a court makes a final determination that the harm resulted from Coinbase’s gross negligence, fraud, willful misconduct, or intentional violation of law.
Coinbase’s allocation of responsibility for account security remains unchanged. The User Agreement places responsibility on users for safeguarding login credentials and expressly disclaims liability for losses resulting from compromised credentials, unauthorized access, or misuse of the Trusted Contacts feature.
Coinbase’s Formal Complaint Process remains unchanged
The User Agreement’s Formal Complaint Process remains unchanged.
Under Section 7.2, users must first attempt to resolve any dispute by contacting Coinbase Support.
If the dispute is not resolved through Coinbase Support, users are required to complete Coinbase’s Formal Complaint Process before filing any arbitration claim under Section 7.3.
Failure to complete the Formal Complaint Process may result in dismissal of the arbitration.
If a dispute proceeds to the Formal Complaint Process, users must submit a complaint using Coinbase’s designated complaint form (or request the form from Coinbase Support), describing the dispute, the requested resolution, and any relevant information.
The Formal Complaint Process is deemed complete when Coinbase responds to the complaint or forty-five (45) business days after Coinbase receives it, whichever occurs first.
Because arbitration cannot be initiated until this process is completed, the Formal Complaint Process serves as a mandatory procedural prerequisite to arbitration under the User Agreement.
For a step-by-step overview of how to comply with Coinbase’s Formal Complaint Process, see:
Arbitration Process Remains Unchanged
The User Agreement’s arbitration provisions also remain unchanged.
Once the Formal Complaint Process is completed, disputes that are not resolved must continue to be pursued through binding arbitration in accordance with the procedures set forth in the User Agreement.
For a detailed, step-by-step overview of how Coinbase arbitration works in practice – including filing requirements, timelines, and procedural considerations – see our previously published guide:
Users should also be aware that the User Agreement continues to include a broad waiver of procedural rights.
Claims against Coinbase must be brought on an individual basis only, and users waive the right to participate in class, collective, or representative actions.
In addition, the User Agreement expressly includes a jury trial waiver, meaning that if any dispute were to proceed in court, it would be resolved by a judge rather than a jury.
The arbitration provisions further permit fee-shifting in limited circumstances. A user may be required to pay Coinbase’s attorneys’ fees and costs if an arbitrator determines that a claim was frivolous or brought for an improper purpose, or if a court finds that the user failed to satisfy required pre-arbitration conditions.
Contact Us
If your Coinbase account was hacked and your crypto was stolen, contact Dilendorf Law Firm to discuss your recovery options and case strategy.
Our team has represented victims in 130+ crypto cyber-theft arbitrations across major forums (AAA, JAMS, NAM), including cases against Coinbase and other leading U.S. exchanges.
The firm focuses on stolen-crypto recovery, SIM-swap and account-takeover cases, and User Agreement–based arbitration claims, integrating blockchain forensics and coordinated law-enforcement engagement where appropriate.
Led by crypto attorney Max Dilendorf (practicing in this space since 2017), the firm represents clients nationwide and internationally in high-stakes exchange disputes.
Email info@dilendorf.com or call (212) 457-9797 to schedule a confidential consultation about your Coinbase theft case.
Domestic Asset Protection Trusts (“DAPTs”) are often criticized as ineffective or vulnerable to creditor attack—especially when the trust creator lives outside the state where the trust is formed.
A recent decision from the Delaware Court of Chancery, however, shows that when properly structured and administered, a Delaware DAPT can withstand aggressive creditor challenges—even when the grantor is a non-resident and the trust indirectly holds valuable real estate.
The case, In the Matter of the CES 2007 Trust, involved a Michigan judgment creditor attempting to reach assets held through a Delaware trust structure. The court rejected those efforts in full and recommended dismissal at the pleading stage.
The Setup: A Michigan Grantor, a Delaware Trust, and Real Estate Held Through LLCs
The trust at issue was created in 2007, years before the underlying Michigan litigation. The grantor was not a Delaware resident. Instead, he used Delaware law to establish a self-settled asset protection trust.
Crucially, the trust did not own real estate directly. Instead, it owned membership interests in Delaware LLCs, and those LLCs owned the real property:
“In pertinent part, the Trust’s assets include a ninety-percent interest in three Delaware limited liability companies…”
Those LLCs, in turn, held real estate in Michigan and Colorado, including residential and commercial properties.
This structure mattered. Under Delaware law:
“A limited liability company interest is personal property. A member has no interest in specific limited liability company property.”
Because the trust owned LLC interests—not the real estate itself—the creditor’s attempt to collapse the structure failed.
Why the Court Refused to “Look Through” the LLCs
The creditor urged the court to disregard the LLC structure, treat the real estate as trust property, and characterize various historical transfers as fraudulent.
The court refused.
It held that it would be inappropriate to adjudicate real estate transactions at the LLC level in an action targeting the trust’s spendthrift provision:
“It would be inappropriate for this Court, through this type of proceeding, to adjudge the real estate transactions at the LLC level under the guise of potential fraudulent transfer sufficient to void the Trust’s spendthrift provision.”
The court went further:
“There are, simply put, no transfers to/from the Trust which would give rise to such an inquiry, and the Petitioner has pled no basis on which this Court should engage in veil piercing.”
This is a critical point for asset protection planning. DAPTs are evaluated based on what the trust owns—not what its subsidiaries own.
Out-of-State Grantors and Delaware Law
Another important aspect of the case is that the grantor was not a Delaware resident. The underlying judgment arose in Michigan. The real estate was located outside Delaware. Yet Delaware law governed the trust.
The court emphasized that Delaware expressly authorizes self-settled asset protection trusts, provided statutory requirements are met:
“In 1997, Delaware codified the ability to create Delaware self-settled asset protection, or qualified disposition, trusts.”
The trust satisfied those requirements, including:
- Invocation of Delaware law
- An enforceable spendthrift provision
- Irrevocability
- Transfers to a qualified trustee
The court found no statutory defect simply because the grantor lived elsewhere.
Trustee Independence and “Control” Arguments
A common creditor argument in DAPT cases is that the grantor retained too much control, effectively acting as the trustee in disguise.
That argument failed here.
The trust had an independent, qualified Delaware trustee. The grantor retained certain advisory powers—but Delaware law expressly permits this.
As the court explained:
“As advisor, the Respondent has the power to manage investments and delegate authority in accordance with his fiduciary duties.”
The court rejected the notion that advisory roles or business management automatically destroy asset protection, noting the statutory framework that allows settlors to appoint advisors and trust protectors.
Common Law Attacks: Public Policy and “Sham Trust” Claims
The creditor also attempted a fallback strategy: arguing that even if the trust met statutory requirements, it should be invalidated under common law doctrines.
Delaware courts recognize that avenue—but apply it narrowly.
The court reiterated that Delaware will not enforce a spendthrift trust that lacks economic reality and exists solely to allow the settlor to enjoy assets without restraint. But that was not the case here.
The court concluded:
“Neither doctrine supports the Petitioner’s request for relief in this action.”
And explicitly declined to recharacterize the structure:
“I decline to pierce down, treat the LLCs as shams or alter egos […] and convert the Trust’s membership interests therein to real property interests.”
The Outcome: Dismissal at the Pleading Stage
After reviewing the trust’s structure, governance, and statutory compliance, the court reached a clear conclusion:
“The Petitioner has failed to state a claim to void the spendthrift provision of the Trust or invalidate the Trust altogether.”
The recommended result:
“The Respondent’s motion to dismiss the Amended Petition should be granted, and the Amended Petition should be dismissed.”
What This Case Means for Asset Protection Planning
This decision reinforces a central principle we emphasize in our asset protection practice: effective planning is not about evasion—it is about structure, discipline, and statutory compliance.
When those elements are present, courts will respect the plan, even under aggressive creditor attack.
At Dilendorf Law Firm, we represent high-risk professionals and entrepreneurs whose personal and professional exposure makes proactive asset protection essential.
We represent physicians, surgeons, medical specialists, real estate developers, builders, business owners, and investors—individuals whose success often places them squarely in the crosshairs of litigation.
The Delaware Court of Chancery’s decision in In the Matter of the CES 2007 Trust underscores several planning principles that are directly relevant to this clientele:
- DAPTs can protect assets even when the grantor lives in another state
- LLC layering matters—owning real estate indirectly can be decisive
- Qualified trustees and statutory compliance are non-negotiable
- Retained advisory powers do not automatically defeat asset protection
At Dilendorf Law Firm, we assist U.S. and non-U.S. clients protect a wide range of assets, including:
- Income-producing and investment real estate
- Operating businesses and development projects
- Investment portfolios (public and private securities)
- Cryptocurrency and digital assets
- Cash reserves and alternative investments
This case also serves as a reminder that timing matters.
The trust in question was established years before the underlying litigation—an essential factor in surviving fraudulent transfer challenges.
Asset protection is most effective when implemented before a claim arises, not in reaction to one.
Ultimately, CES 2007 confirms what sophisticated planners already understand: well-designed Delaware DAPTs—combined with disciplined administration and proper entity structuring—remain a powerful tool for protecting wealth against future creditor risk.
For high-exposure professionals and investors, asset protection is not a luxury. It is a core component of long-term financial and estate planning—and when done correctly, courts will enforce it.
Contact Us
At Dilendorf Law Firm, we assist U.S. and international clients with sophisticated cross-border estate and asset protection planning. Our practice spans domestic asset protection trusts (DAPTs) in leading U.S. jurisdictions—such as Wyoming, Alaska, Nevada, and South Dakota—as well as offshore trust structures in key jurisdictions including the Cook Islands, Nevis, and the Cayman Islands.
In each jurisdiction, we have developed a network of experienced trustees, financial institutions, and vetted legal partners who help ensure that every structure is professionally administered and compliant with local regulatory standards.
To discuss how our experience and network can support your planning goals, contact us at info@dilendorf.com or by calling us at 212.457.9797 to discuss your needs.